[ad_1]
Cybersecurity researchers have published two concerning reports where the first report highlights the surge in cyber attacks against the aviation and aerospace industries – And the second report exposes a dark web tool called TMChecker fueling attacks against E-commerce platforms.
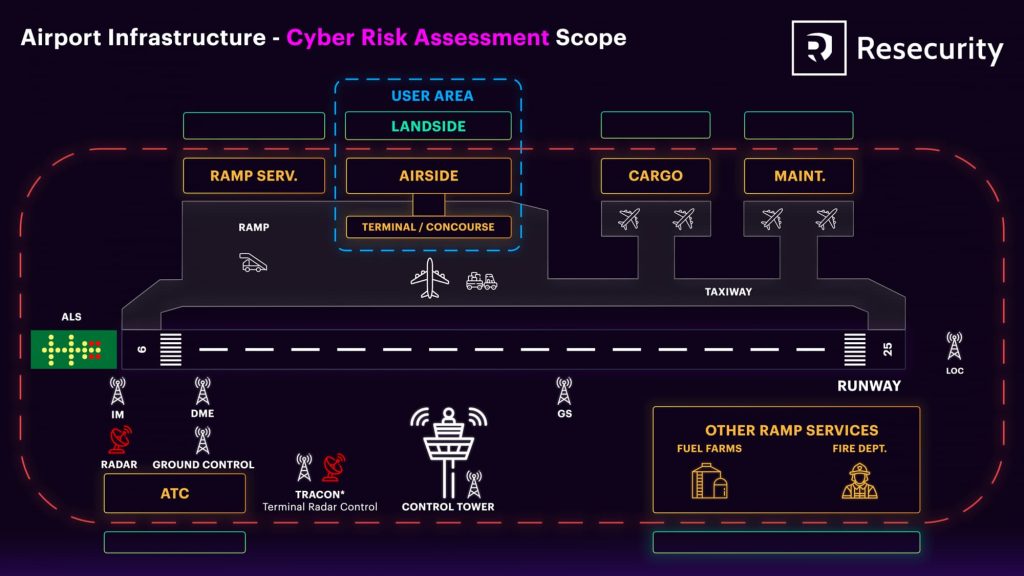
Recent cyber incidents targeting the aerospace and aviation sectors have raised concerns about the industry’s vulnerability to malicious attacks, according to a report by Resecurity. The report highlights the critical need for strong cybersecurity risk assessments to protect airports and aviation infrastructure.
The aerospace sector, including the design, manufacturing, and maintenance of aircraft and spacecraft, has become a prime target for cyberattacks due to its reliance on interconnected digital infrastructures and global supply chains.
The integration of Industrial Internet of Things (IIoT) technologies has further strengthened this threat, making aerospace organizations more vulnerable and susceptible to cyber attacks.
Ransomware Attacks & The Aviation Industry
Ransomware emerges as a top threat facing the aviation industry, with a 600% increase in occurrences reported by Boeing Chief Security Officer Richard Puckett at the 2023 Aviation Week MRO Americas Conference.
The European Organisation for the Safety of Air Navigation (Eurocontrol) also highlighted ransomware as the sector’s leading attack trend in 2022, accounting for 22% of all malicious incidents. Some of the examples highlighted in the report include the LockBit ransomware gang’s attack on Boeing in November 2023, which the aviation giant later confirmed.
Geopolitical tensions & The Aviation Industry
According to Resecurity’s blog post titled “The Aviation And Aerospace Sectors Face Skyrocketing Cyber Threats,” geopolitical tensions and the designation of aerospace and aviation as critical infrastructure by the U.S. government have fueled cyberattacks targeting the industry.
Threat actors, including hacktivist collectives, are increasingly targeting aviation organizations to advance political agendas or disrupt operations. One such example is the hacktivist group Anonymous Sudan which targeted FlyDubai, an Emirati government-owned airline in Dubai, United Arab Emirates in February 2024 citing the company’s alleged support to the Rapid Support Forces (RSF) in Sudan.
Other recent cyberattacks targeting the aerospace sector include Distributed Denial of Service (DDoS) attacks by groups such as Mysterious Team Bangladesh (MTB) against Saudi Arabian airports and ALTOUFAN TEAM against Gulf Air.
In stand with our steadfast Palestinian people in Gaza Strip in their brave and honorable resistance,ALTOUFAN TEAM targets companies normalized with the Zionist entity , Bahrain International Airport and the Bahraini national carrier “Gulf Air” servers and website…… pic.twitter.com/OKOhR12M3S
— ALTOUFAN TEAM (@altoufanteam) November 22, 2023
Additional incidents involve ransomware attacks on airlines like Air Albania and Continental Aerospace Technologies, compromising critical data and disrupting operations.
TMChecker – Dark Web Tool Targeting Remote Access and E-Commerce Platforms
In another report published on March 13, 2024, Resecurity detailed a new cybersecurity threat named TMChecker that has surfaced on the Dark Web, posing a notable risk to remote-access services and popular e-commerce applications.
Developed by an actor known as “M762” on the Russian language XSS cybercrime forum, TMChecker is a sophisticated tool that combines corporate access login (log) checking capabilities with a brute-force attack kit. Available for a monthly subscription fee of $200, TMChecker has garnered attention for its ability to target a wide range of VPN gateways, email servers, and e-commerce platforms.
TMChecker stands out from similar tools like ParanoidChecker due to its focus on corporate remote access gateways, which are often primary targets for ransomware attacks and other malicious activities. The tool supports 17 solutions, including Cisco VPN, Citrix VPN, Office 365, WordPress, Magento, and cPanel, among others, making it a versatile and powerful weapon.
Cybercriminals exploit TMChecker to identify compromised data containing valid credentials for corporate VPN and email accounts. In one observed incident, threat actors used TMChecker to target the email server of a government organization in Ecuador, demonstrating the tool’s real-world impact.
M762 operates a Telegram channel with over 3,270 subscribers, potentially indicating a sizable user base for TMChecker. The addition of such tools aligns with a concerning trend highlighted in recent Microsoft research, which noted a significant increase in human-operated ransomware attacks.
These attacks often involve the abuse of remote monitoring and management tools, leaving behind less evidence compared to automated attacks delivered through malicious documents.
As TMChecker and similar tools lower the barriers to obtaining remote access credentials, the risk of destructive ransomware attacks and other malicious campaigns amplifies. This threat is particularly acute in the context of mergers and acquisitions, where cybercriminals target vulnerable organizations to exploit for financial gain.
RELATED TOPICS
- Cl0p ransomware gang hits Aviation giant Bombardier
- Hackers Uncover Airbus EFB App Flaws, Risking Aircraft Data
- Israeli: Hackers Targeted EL AL Flights in Mid-Air Hijack Attempt
- Military Satellite Access Sold on Russian Hacker Forum for $15,000
- Hackers posing as LinkedIn recruiters to scam military, aerospace firms
[ad_2]
Source link