[ad_1]
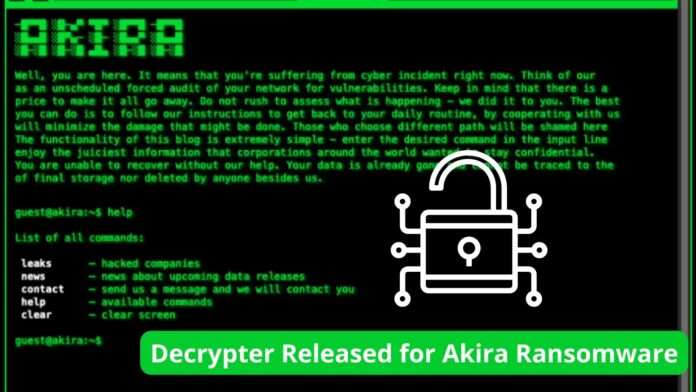
Akira ransomware appeared in 2017 when it encrypted video folders without leaving any ransom notes. The file encrypted by Akira ransomware has an extension of .akira.
Researchers have been working on decrypting the files affected by the ransomware and finally got a breakthrough.
Researchers at Avast have found a way to decrypt the files affected by the Akira ransomware. Avast has also released the 64-bit as well as 32-bit versions of the decryptor tool for users.
Technical Analysis of Akira Ransomware
The ransomware has affected education, finance, real estate, and many other organizations.
Akira ransomware is specifically built for Windows Platforms as it uses 64-bit Windows binary for encrypting the files. It is written in C++ and uses a lot of C++ libraries.
Akira uses symmetric encryption, which has an encryption key generated by the CryptGenRandom() function by Windows CryptAPI, and uses ChaCha 2008 for encrypting the files on the affected systems.
However, the ransomware has also affected Linux operating systems and uses the Crypto++ library as a replacement for Windows CryptAPI.
By default, the ransomware excludes certain folders and file extensions from encrypting, which includes,
Files
- .exe
- .dll
- .lnk
- .sys
- .msi
- Akira_readme.txt
Folders
- winnt (default installation folder of Windows 2000)
- temp
- thumb
- $Recycle.bin
- $RECYCLE.BIN
- System Volume Information
- Boot
- Windows
- Trend Micro
Akira Ransomware Vs Conti Ransomware
There seem to be a lot of similarities between the Conti V2 Ransomware and the Akira ransomware. This can be due to the authors’ inspiration from the Conti.
The list of excluded files and folders, the structure of the file tail, the use of ChaCha 2008, and the use of CryptGenRandom and CryptEncrypt appears to be much similar to Conti Ransomware.
Avast is currently working on the decryptor tool for its Linux Version.
Just like any other ransomware, the ransom notes provide two tor websites: the payment site and the list of victims site (shows the list of Akira ransomware victims).
Avast has provided a complete report and instructions on how to use this tool. Users have to download the decryptor tool (32-bit or 64-bit) from the Avast website and run it as an administrator, which will fire up the Wizard for decryption.
Users must submit two identical files, one of which must be an original file and the other the same file affected by Akira ransomware with the extension (.akira).
The tool takes some time to get the password for decrypting the files. In the end, the tool also asks for backing up the decrypted files using the wizard.
The ransomware was using a symmetric RSA-4096 cipher encryption key that was appended at the end of the file while the public key was hardcoded inside the ransomware binary.
“AI-based email security measures Protect your business From Email Threats!” – Request a Free Demo.
[ad_2]
Source link

.png
)