[ad_1]
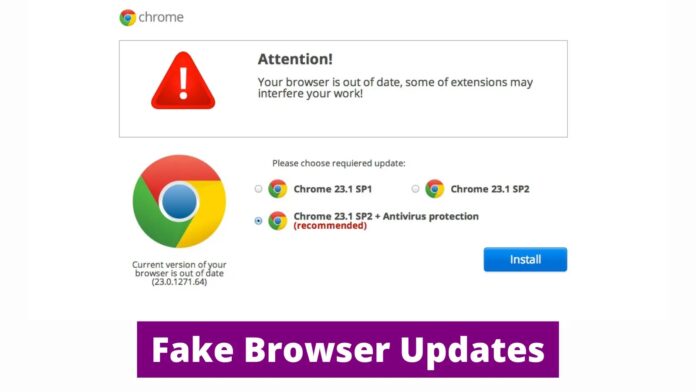
SocGholish malware, also known as FakeUpdates, has exhibited new behavior since July 4th, 2024, as the infection chain still begins with a compromised website prompting a fake browser update.
Downloading the update triggers malicious code that fetches additional malware. Unlike prior campaigns where SocGholish installed common RATs, recent attacks involved the execution of additional files and scripts, deviating from the usual patterns.

The initial malicious Javascript downloads a PowerShell script that bypasses AMSI and fetches the next stage loader from a DGA-generated domain.
Protect Your Business Emails From Spoofing, Phishing & BEC with AI-Powered Security | Free Demo
This second stage decodes, decrypts, and decompresses a third-stage PowerShell script using a Base64 encoded string, a hardcoded XOR key, and Gzip compression. The functionality can be replicated in CyberChef to reveal the final AsyncRAT payload.
.webp)
Stage 3 of the AsyncRAT malware uses various techniques to detect virtualized environments, which check for specific strings in system information like “VMware” or “VirtualBox” and assign scores.
A higher score indicates a higher likelihood of being in a virtual machine, and the final score is then incorporated into a cURL request parameter along with a randomly generated domain name fetched by the Domain Generation Algorithm (DGA).
If the score passes the threshold on the C2 server, the final AsyncRAT payload is delivered.
.webp)
A malicious PowerShell script disguised as a BOINC software installation uses cURL to download a file and then creates a random directory and file name, downloads a ZIP archive, extracts it, renames a file likely containing malware (BOINC.exe), and creates a scheduled task to execute it.
To potentially evade detection, the script removes itself and creates a registry value with a misspelled key name (“ExpirienceHost”) as a possible infection marker.
.webp)
SocGholish malware is abusing BOINC, an open-source distributed computing software, to create a command-and-control (C2) server by installing a disguised BOINC client that connects to a malicious server instead of legitimate BOINC servers.
While no malicious tasks have been observed yet, the attacker can potentially steal information, transfer files, or execute further malware on the infected hosts.
.webp)
An AsyncRAT infection was discovered through the analysis of scheduled tasks, which include malicious PowerShell commands disguised within log file names and executed by a headless Conhost process.
It establishes persistence for the AsyncRAT and maintains connections to its C2 server, and tasks associated with a BOINC client were found, which may be a downloaded component for cryptocurrency mining or other purposes.
According to Huntress, the techniques used in this attack closely resemble those linked to the SocGholish malware family, particularly its use of fake browser updates for initial access and obfuscated PowerShell downloads for AsyncRAT deployment.
Join our free webinar to learn about combating slow DDoS attacks, a major threat today.
[ad_2]
Source link