[ad_1]
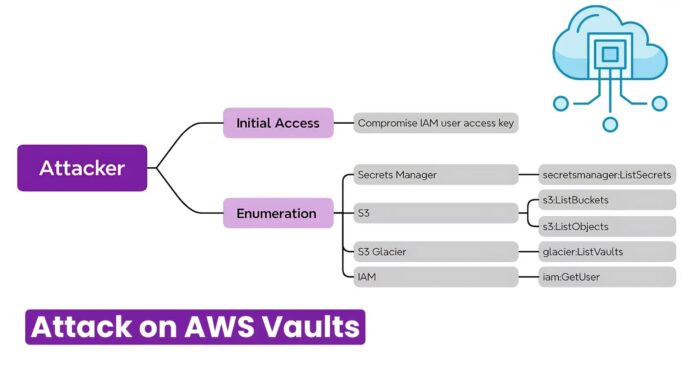
Hackers target vaults, buckets, and secrets to access some of the most classified and valuable information, including API keys, logins, and other useful data kept within these storage solutions.
These storage solutions’ centralized and often inadequately protected nature makes them exceptional targets for the threat actors.
Cybersecurity analysts at DATADOG Security Labs discovered that hackers have been attacking the vaults, buckets, and secrets to steal data.
Hackers Attacking AWS Vaults
From 2024-05-23 to 2024-05-27, analysts detected abnormal behavior in a client’s AWS during threat hunting. IP 148[.]252.146.75 attempted ListSecrets and ListVaults API calls.
Enriched as a potential UK Vodafone residential proxy. Activity in another AWS included ListBuckets to enumerate S3 buckets, then ListObjects on available buckets – automated per event times.
Free Webinar on API vulnerability scanning for OWASP API Top 10 vulnerabilities -> Book Your Spot
No GetSecretValue, BatchGetSecretValue, or GetObject were observed despite the S3 data events that were enabled. While the reasons are:-
- Broad automated campaign assessing available data before exfiltration
or
- Testing AWS identity access level for resale value determination
First, the attacker was observed targeting the S3 Glacier vault backup data. After failed enumeration, subsequent InitiateJob calls were expected to retrieve the vault archive list and specific archive, then GetJobOutput to download.
Attackers commonly mask location using VPNs like free Cloudflare WARP, whose AWS API calls may seem less suspicious than other VPN providers.
.webp)
The requests-auth-aws-sigv4 Python library likely generated the identified user agent for manually signing AWS API requests, unlike typical AWS CLI or Boto3 SDK usage, which handles Sigv4 signing automatically.
Manually managing to sign provides no real advantage but could indicate suspicious activity if unexpected in your environment.
Recommendations
Researchers recommend detection and response teams closely examine this campaign due to the potentially severe operational impact of the exfiltration of production LLM data and resources from your cloud environment.
Here below, we have mentioned all the detection opportunities:-
- Utilize IoCs to detect specific campaigns.
- Enrich CloudFlare IPs if expected API calls.
- Multiple regions ListSecret/ListVault in a short period.
- 17 regions under 1 minute in observed data.
- Spikes in AccessDenied for ListSecrets, ListBuckets, ListObjects, ListVaults.
- Suspicious AccessDenied spikes indicate a lack of proper permissions.
Free Webinar! 3 Security Trends to Maximize MSP Growth -> Register For Free
[ad_2]
Source link