[ad_1]
CloudGrappler is an innovative open-source tool designed to detect the presence of notorious threat actors in cloud environments.
This tool is a beacon of hope for security teams struggling to keep pace with the sophisticated tactics of groups like LUCR-3, also known as Scattered Spider.
CloudGrappler leverages the power of CloudGrep, a tool developed by Cado Security, to offer high-fidelity, single-event detections of activities associated with well-known threat actors in popular cloud platforms such as AWS and Azure.
It acts as a cyber detective, sifting through the vast amounts of data in cloud environments to identify suspicious and malicious activities that often go unnoticed.
Key Features of CloudGrappler
- Threat Actor Querying: CloudGrappler excels in identifying activities demonstrated by some of the most notorious cloud threat actors. It utilizes a subset of activities from Permiso’s extensive library of detections to help organizations pinpoint threats targeting their cloud infrastructure.
- Single-Event Detections: The tool provides a granular view of potential security incidents, enabling security teams to quickly and easily identify specific anomalies within their AWS and Azure environments.
- Integration with CloudGrep: By incorporating a set of Tactics, Techniques, and Procedures (TTPs) observed in the modern threat landscape, CloudGrappler enhances its threat detection capabilities.
Malware analysis can be fast and simple. Just let us show you the way to:
- Interact with malware safely
- Set up virtual machine in Linux and all Windows OS versions
- Work in a team
- Get detailed reports with maximum data
If you want to test all these features now with completely free access to the sandbox:
How CloudGrappler Works
CloudGrappler includes several components designed to streamline the threat detection process:
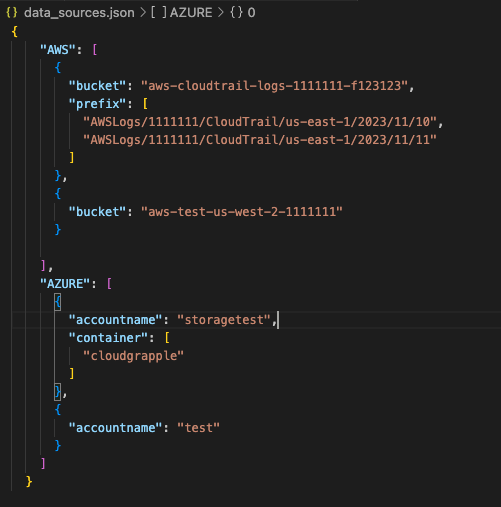
- Scope Selector: Users can define the scope of their scanning through an integrated data_sources.json file, choosing to scan specific resources or a broader range of cloud infrastructure services.
- Query Selector: The tool comes with a queries.json file containing predefined TTPs commonly used by threat actors. Users can modify these queries or add custom ones to tailor the scanning process.
- Report Generator: After scanning, CloudGrappler produces a comprehensive report in JSON format, offering detailed insights into the scan results and enabling security teams to address potential threats swiftly.
It is based on a subset of activity from Permiso’s library of hundreds of detections, and it helps organizations detect threats targeting their cloud infrastructure.
Practical Applications
CloudGrappler is not just about detecting suspicious activities. it also provides valuable threat intelligence to help security professionals understand the risks in their environment and develop targeted response strategies.
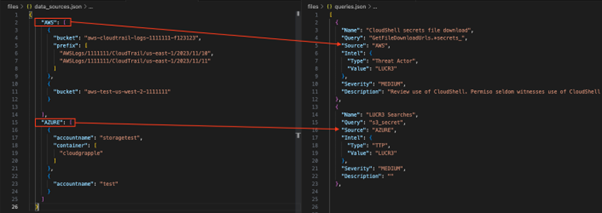
The tool’s output includes information on the threat actor involved, the severity of the detected activity, and a description of the potential implications.
For those interested in enhancing their cloud security posture, CloudGrappler is available on GitHub.
The repository includes detailed instructions on setting up and using the tool, making it accessible to security teams of all sizes.
As cloud environments become increasingly complex and threat actors’ activities more sophisticated, tools like CloudGrappler are essential for maintaining a robust security posture.
CloudGrappler represents a significant step forward in the fight against cybercrime by offering an open-source solution for detecting and analyzing threats in cloud environments.
You can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits, with Perimeter81 malware protection. All are incredibly harmful, can wreak havoc, and damage your network.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter
[ad_2]
Source link
