[ad_1]
KEY FINDINGS
- Group-IB uncovers cryptojacking campaign on popular thesaurus site.
- Attackers used a drive-by-download technique to spread malware.
- The campaign distributed a Monero cryptocurrency miner.
- Unsophisticated tactics highlight risks even on trusted websites.
- Recommendations emphasize the importance of regular updates and robust security measures.
Cybersecurity researchers at Group-IB unearthed a covert cryptojacking campaign concealed within a popular online thesaurus boasting over five million monthly visitors. This campaign employed a cunning tactic, embedding a script that surreptitiously installed malware on visitors’ computers to mine cryptocurrency, opening the door for more malicious activities.
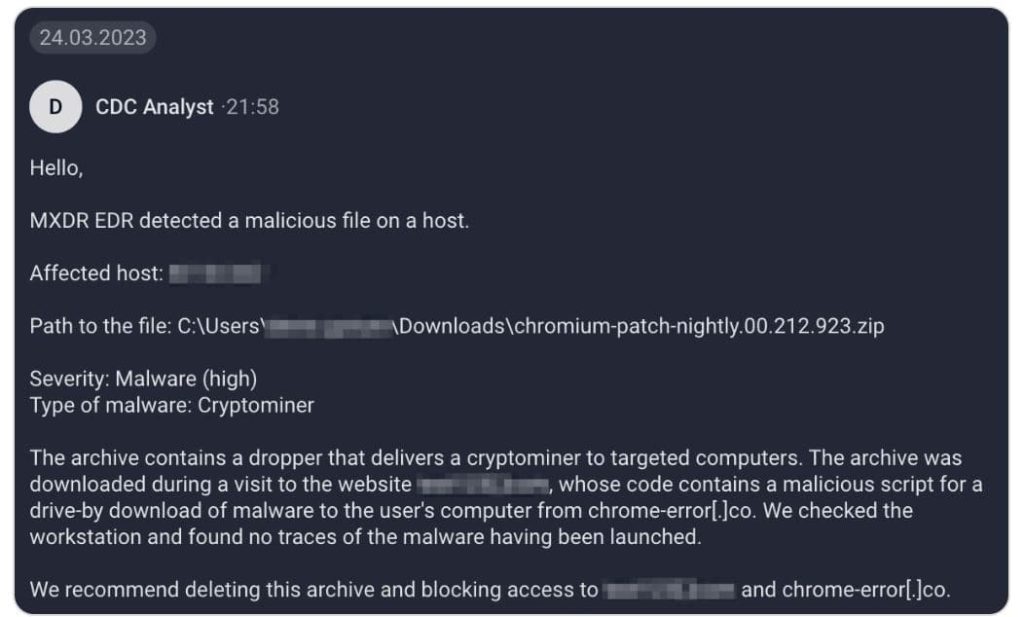
Group-IB’s experts crack the story behind this cybercriminal operation through their use of Managed Extended Detection and Response (MXDR), a solution designed for round-the-clock threat monitoring, proactive threat hunting, and real-time attack mitigation.
During their monitoring, Group-IB’s security specialists detected numerous malicious archives flagged by the MXDR system. This triggered an alarm as they observed an unusually high number of malware samples emerging within the infrastructure of several client companies.
These archives, peculiarly named in the pattern of “chromium-patch-nightly.00.{3}.{3}.zip,” each with a unique identifier, indicated that the MXDR customers had received these malicious archives from a common source, suggesting an unconventional approach taken by the attackers.
Upon analyzing these malicious archives; Group-IB found that they contained an executable file functioning as a dropper, responsible for installing the XMRig Coinminer—a cryptocurrency mining tool specifically designed for Monero. Monero’s inherent anonymity, which conceals transaction details, allows threat actors to remain covert.
To trace the source of these infected archives, Group-IB turned to data from the Endpoint Detection and Response (EDR) module. After analyzing the events related to the discovery of the malicious objects on host machines, it was apparent that the archives had been downloaded to the “Downloads” folder, typically used by default during user internet sessions. The security experts examined browser history, revealing that these malicious samples were downloaded from an online thesaurus.
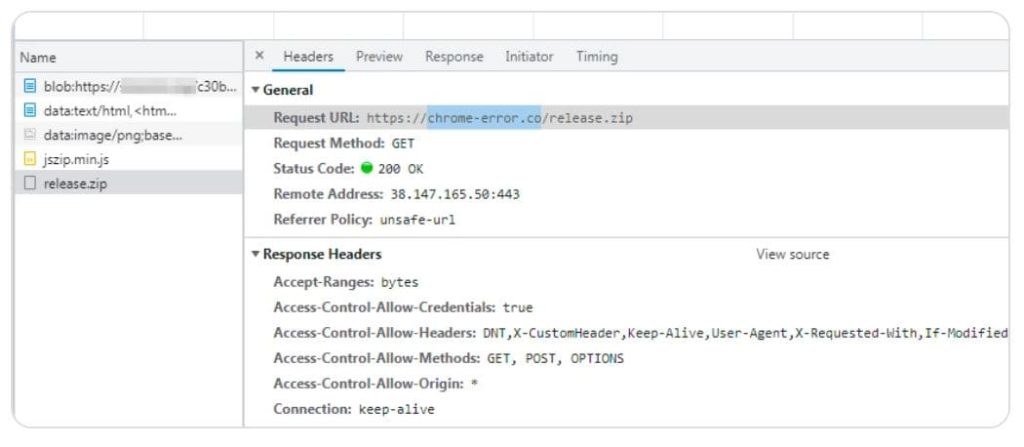
Group-IB’s analysts reconstructed the infection chain, revealing that when visitors accessed the thesaurus website, a decoy page triggered the automatic download of a malicious archive. Notably, the script responsible for this action was not injected into the section of the website dedicated to antonyms. The archive itself was downloaded from another website, chrome-errorco.
Further investigation revealed that the dropper, despite being downloaded to users’ machines, had not been executed, preventing any immediate threats.
According to Group-IB’s report, to safeguard their clients from potential security incidents, Group-IB promptly notified them about the threat. Additionally, the experts shared contextual insights about the incident and recommended preventive measures, including the deletion of the malicious archive.
In the event of confirmed malicious files, Group-IB MXDR’s Endpoint Detection and Response (EDR) agent is capable of automatically blocking and locally quarantining such files.
Despite the ability of Group-IB MXDR to block known malicious files, the system sends periodic requests to the main console, sharing hashes of files marked as malicious by the behavioral analysis subsystem. This feature ensures that if one customer detects a malicious file, the hash is subsequently added to other customers’ blocklists.
The analyzed script responsible for the attack conducted the following actions:
Sent a signal to a specified page and downloaded a new script, executing it
Displayed a fake Chrome error page instructing users to install a downloaded update
Ultimately, this revelation underscores the critical need for vigilance even on trusted and highly frequented websites.
The cybercriminals behind this campaign employed well-known tactics, such as drive-by downloads and social engineering via deceptive error pages, emphasizing the importance of robust cybersecurity measures.
Group-IB’s analysis further revealed that the threat actors’ relatively unsophisticated approach should not be underestimated. Once the loader infiltrates a target company’s infrastructure, it can serve as a potent vector for future, more damaging attacks beyond cryptocurrency mining, such as ransomware or wipers, which can result in severe disruptions and significant damage.
For secure defences against such threats, Group-IB recommends:
- Keeping operating systems and software up to date
- Downloading software and updates from official sources or restricting user rights to update independently
- Monitoring workstation resource utilization for signs of cryptomining activity
- Employing Endpoint Detection and Response solutions to block malicious file downloads and halt attacks at their earliest stages
- Utilizing modern Malware Detonation Platforms for safe and thorough analysis of suspicious files
RELATED ARTICLES
Infected WAV files install malware & cryptominers on PCs
Group-IB Founder Ilya Sachkov Jailed for 14 Years in Russia
VictoryGate cryptominer infected 35K devices via USB drives
Crypto Miner Hiding in Fake Microsoft, Google Translate Apps
WinRAR users update software as 0-day vulnerability is found
[ad_2]
Source link