[ad_1]
Shopify has denied a breach of its systems after a cybercriminal posted alleged Shopify customer details online.
Shopify told BleepingComputer and other publications that the incident happened at a third party:
“Shopify systems have not experienced a security incident. The data loss reported was caused by a third-party app. The app developer intends to notify affected customers.”
The cybercriminal posting under the handle “888” claims the breach took place in 2024 and contains 179,873 rows of users’ information.
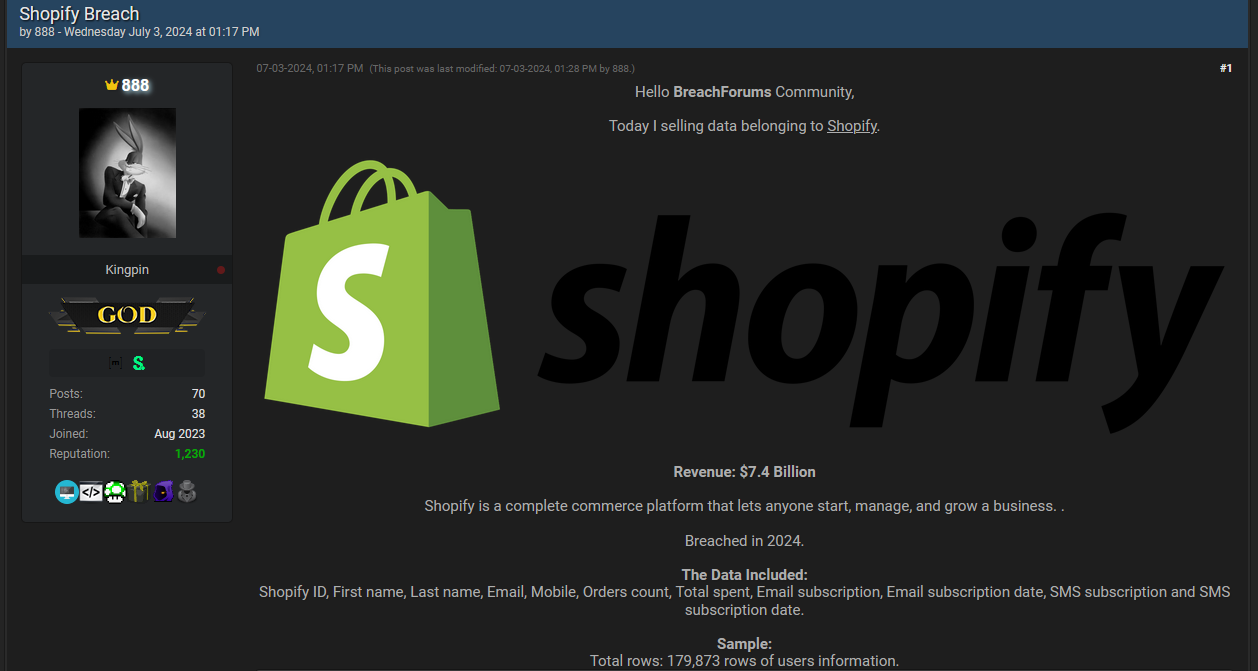
The data offered for sale includes:
- Shopify ID
- First name
- Last name
- Email address
- Mobile phone number
It also includes some Shopify specific data like number of orders, total spent, email subscription status, email subscription date, SMS subscription status, and SMS subscription date.
Where the data comes from is a good question.
In March, Cybernews reported about a publicly accessible MongoDB database that belonged to a US-based company, Saara, who develop Shopify plugins. The leaked database stored 25GB of data which stemmed from plugins covering over 1,800 Shopify stores.
In June, we reported about a breach affecting Evolve Bank & Trust that also affected several of its partners. Shopify is a partner of Evolve.
No doubt this isn’t the end of the story. We will keep you updated.
Protecting yourself after a data breach
There are some actions you can take if you are, or suspect you may have been, the victim of a data breach.
- Check the vendor’s advice. Every breach is different, so check with the vendor to find out what’s happened, and follow any specific advice they offer.
- Change your password. You can make a stolen password useless to thieves by changing it. Choose a strong password that you don’t use for anything else. Better yet, let a password manager choose one for you.
- Enable two-factor authentication (2FA). If you can, use a FIDO2-compliant hardware key, laptop or phone as your second factor. Some forms of two-factor authentication (2FA) can be phished just as easily as a password. 2FA that relies on a FIDO2 device can’t be phished.
- Watch out for fake vendors. The thieves may contact you posing as the vendor. Check the vendor website to see if they are contacting victims, and verify the identity of anyone who contacts you using a different communication channel.
- Take your time. Phishing attacks often impersonate people or brands you know, and use themes that require urgent attention, such as missed deliveries, account suspensions, and security alerts.
- Consider not storing your card details. It’s definitely more convenient to get sites to remember your card details for you, but we highly recommend not storing that information on websites.
- Set up identity monitoring. Identity monitoring alerts you if your personal information is found being traded illegally online, and helps you recover after.
Malwarebytes has a free tool for you to check how much of your personal data has been exposed online. Submit your email address (it’s best to give the one you most frequently use) to our free Digital Footprint scan and we’ll give you a report and recommendations.
[ad_2]
Source link
