[ad_1]
SMS scammers are using cloud storage from Google, Amazon, and IBM to trick you! Learn how they’re doing it and how to protect yourself from these sneaky cloud phishing scams.
The threat intelligence unit at Enea, a software security firm based in Stockholm, Sweden, has uncovered a concerning trend: cybercriminals are exploiting cloud systems to perpetrate SMS scams including Smishing or SMS phishing.
According to the investigation by the company’s threat intelligence team, cloud storage services like Amazon S3, Google Cloud Storage, Backblaze B2, and IBM Cloud Object Storage are being exploited to redirect users to malicious websites, stealing their information through SMS.
How Cloud Storage is Exploited?
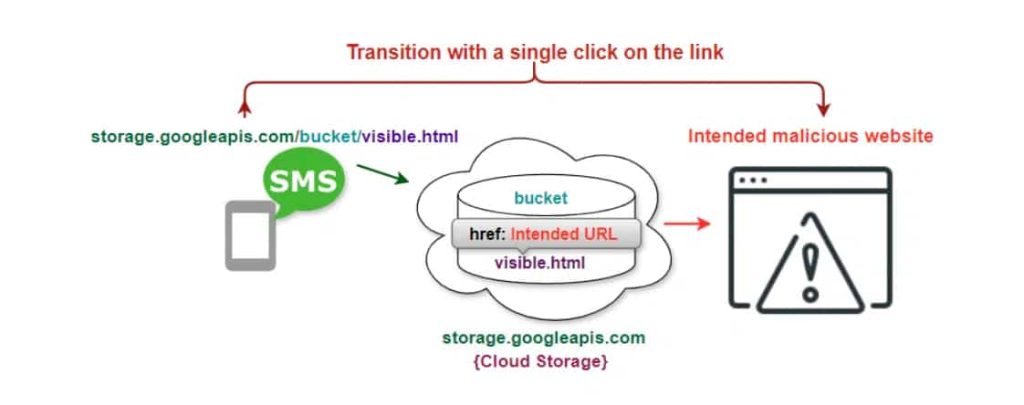
Cloud storage allows organizations and individuals to store, access, and manage files, including static websites. However, cybercriminals have exploited this facility to host static websites with embedded spam URLs in their source code.
These URLs are distributed via authentic text messages, bypassing firewall restrictions. Mobile users click on links containing cloud platform domains, which direct them to the static website stored in the storage bucket, automatically forwarding or redirecting them without user awareness.
The Scam: From SMS to Fake Websites
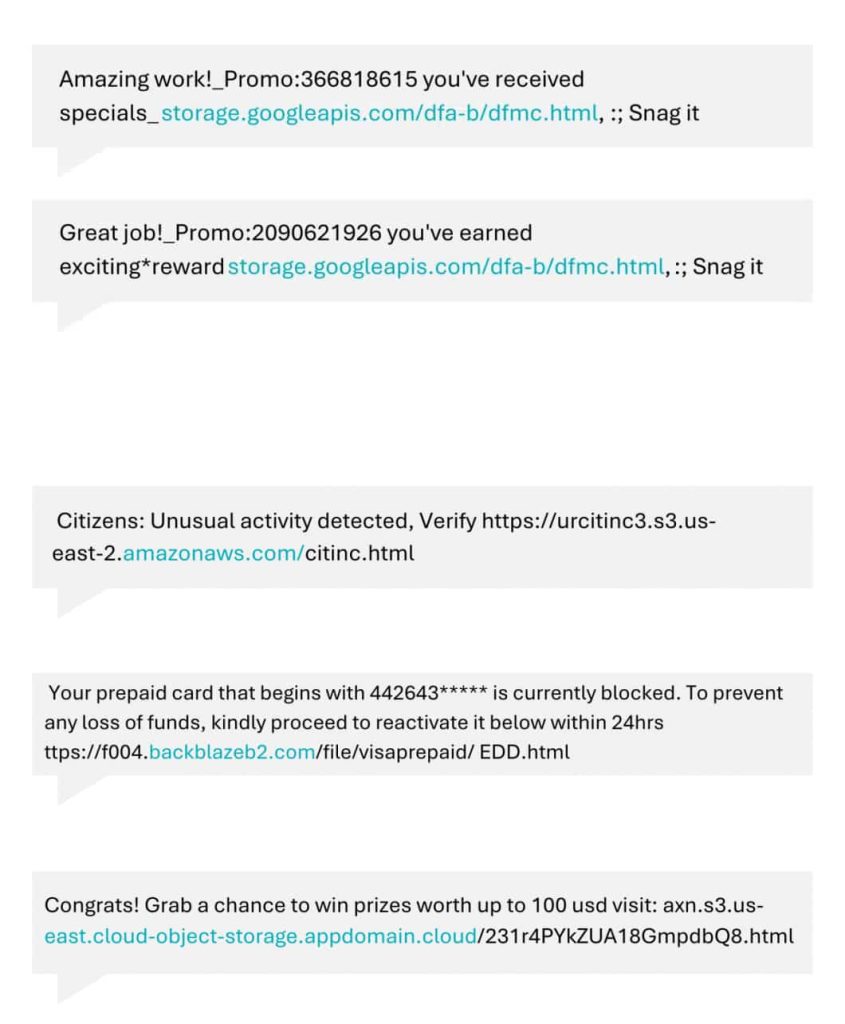
According to Enea’s blog post that the company shared with Hackread.com ahead of publication on Thursday 23rd, 2024, the attackers prioritize two main objectives: delivering scam messages without network firewall detection and convincing end users to perceive the messages or links as trustworthy.
The scam starts with a seemingly harmless text message (SMS). These messages often contain enticing offers or create a sense of urgency, tricking recipients into clicking a link. This link redirects them to a malicious website cleverly disguised as a legitimate one.
As per the research, Google Cloud Storage’s domain, “storage.googleapis.com,” is used by attackers to link to a static webpage hosted in a bucket on the platform. The spam website is loaded from that webpage using the “HTML meta refresh” method, a technique used in web development to automatically refresh or redirect a web page after a certain time period.
These fake websites, typically hosted on cloud storage buckets with names like “dfa-b.html” on Google Cloud Storage, aim to steal personal and financial information once users enter it. Users are directed to fraudulent websites offering gift cards to trick users into revealing personal and financial information.
These SMS scammers have also been observed using links to static websites hosted on Amazon Web Services (AWS), IBM Cloud, and Blackblaze B2 Cloud.
Mitigation Strategies
Detecting and blocking URLs containing genuine Google Cloud Storage domains is challenging due to their association with legitimate domains from reputable companies. To protect yourself from cloud phishing scams, be cautious with suspicious SMS links, check website legitimacy before entering personal information, and enable multi-factor authentication (MFA) to add an extra layer of security.
RELATED TOPICS
- The Top 5 Cloud Vulnerabilities You Should Know Of
- Cloud security – An ongoing struggle to keep sensitive data safe
- New Vulnerability LeakyCLI Leaks AWS, Google Cloud Credentials
- Shadow IT: Personal GitHub Repos Expose Employee Cloud Secrets
- Dropbox Abused in New Phishing, Malspam Scam to Steal SaaS Logins
[ad_2]
Source link