Whether you’re a large or small business, network security is something you can’t ignore.
Threat actors can and will, infiltrate businesses of any size wreaking havoc on computer systems, maliciously encrypting data, and in some cases completely destroying a company’s ability to stay in business.
While the latter situation isn’t that common, there have been several recent instances where poor network security has led to significant security breaches.
Consider the Uber breach QAwZ from September 2022, where an MFA fatigue attack led to a breach of Uber’s systems.
A similar attack led to a breach of CISCO’s systems, and Activision ended up being hacked after an SMS phishing attack, which reportedly led to a significant data breach of Activision’s IP and employee data.
These breaches signal the need for better network security practices, and they also show how single security measures are not enough.
All of the breaches mentioned above happened because of a weakness in each company’s MFA practices, but they could’ve been mitigated by other security measures including zero trust granular access rules.
Organizations of all sizes need a network security strategy with modern, cloud-based tools and technologies to stay secure:
Single Sign-On (SSO) with Multi-Factor Authentication (MFA)
Before we even get to network security, organizations should deploy a Single Sign-On (SSO) identity provider with Multi-Factor Authentication (MFA) support.
SSO allows users to access multiple applications using one login.
This makes it easier for users to integrate network security practices into their daily routine without much friction, while the IT team has a much easier time keeping everyone organized.
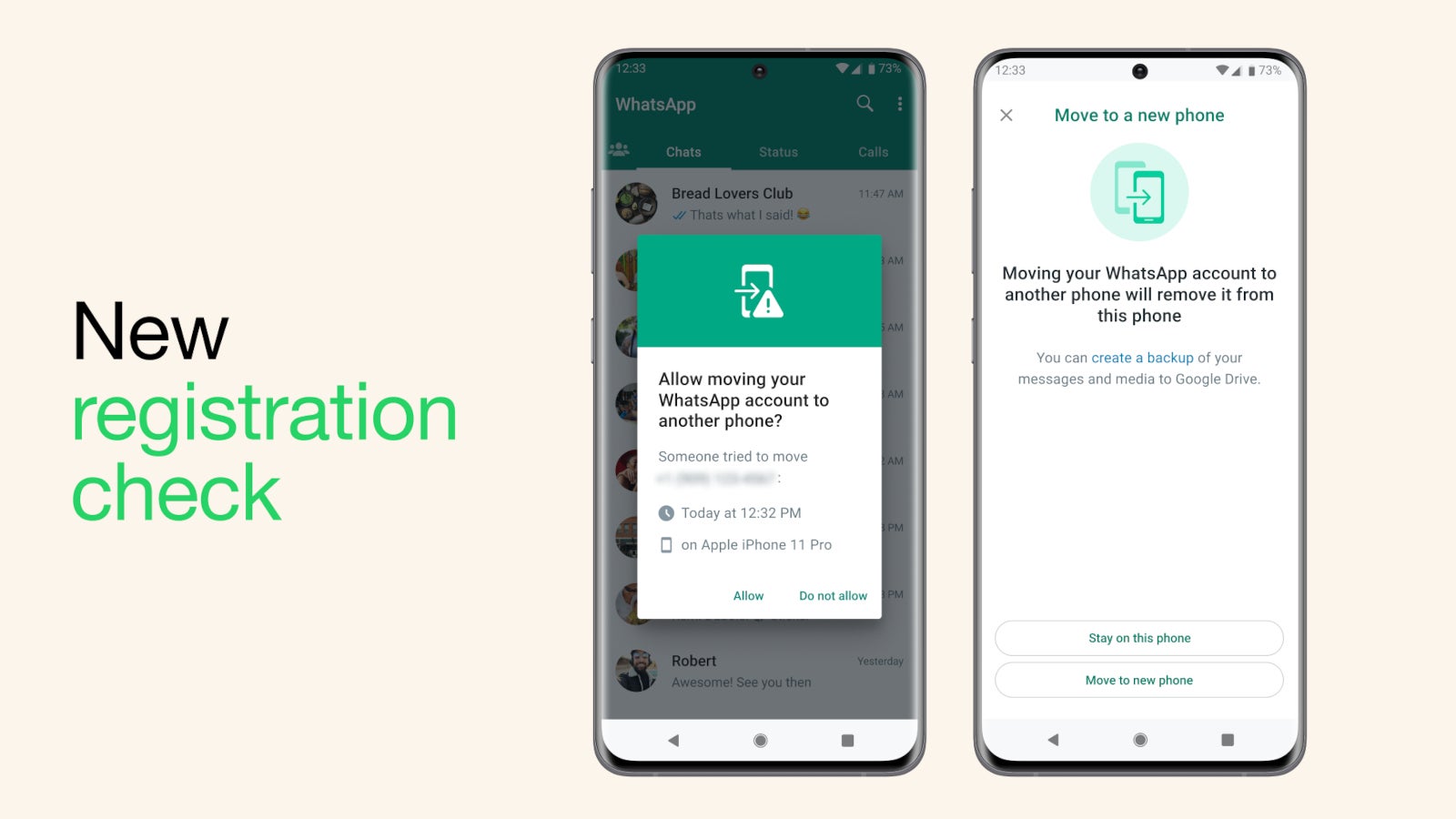
MFA, meanwhile, adds an extra layer of security by requiring users to provide two or more pieces of evidence to prove their identity.
This is typically a username and password, followed by a one-time code, or biometric authentication such as a fingerprint or facial recognition.
Under an MFA scheme, you can require just a second authentication factor or multiple depending on the level of security you need and your threat model.
SSO with MFA also reduces the risk of password-related security incidents, such as password theft or reuse.
It also makes it harder for hackers to access your network since they have to not only steal the password but somehow obtain the second or even third factor to finally break in.
But as we mentioned at the beginning of this article there are ways to get around MFA security measures, so how do you make sure that doesn’t happen?
It starts with training and clearly defined policies that convey to employees that IT teams and outside security contractors will never ask them for their MFA security codes.
Second, you can increase the difficulty of MFA for higher privileged accounts such as a number-based challenge that requires the user to see both sets of numbers to correctly answer the MFA challenge.
Biometric measures can also be effective as long as employees understand they should never authorize an MFA request they didn’t initiate.
Zero Trust Network Access (ZTNA)
One of the biggest and most important strategies in modern network security is the deployment of Zero Trust Network Access. ZTNA assumes that all network traffic is untrusted, even if it originates from inside the network itself.
ZTNA requires that users prove their identity, and then meet specific security requirements before accessing network resources.
This includes granular access rules that can be user- or group-specific. Then context-based verification allows organizations to limit access to resources based on specific criteria, such as device posture, location of the user requesting access, and time of day.
These contexts are also continually verified to ensure that a user’s security posture doesn’t suddenly change, which can be an indication of malicious activity.
Device posture is an important part of context since it demands that user devices meet certain security requirements before accessing resources.
This can be criteria such as the presence of a specific antivirus suite, a custom security certificate, and a minimum operating system version, among others.
When you put it all together Zero Trust Network Access reduces the risk of unauthorized access to sensitive data and resources.
This is a far better approach than the legacy-based VPN and firewall. Under the old model, you would log in with a VPN, and then once you had access to company resources that was it.
There were limited access rules about who could see what and no context-based requirements with continuous verification.
That meant that once a hacker gained access to a system they had an easier time achieving lateral movement (moving from one server or resource to another).
After lateral movement, hackers would often obtain higher privileged account credentials ultimately gaining access to employee and customer data, or sensitive trade secrets.
ZTNA provides better control over network access, which enables organizations to detect and respond to security incidents more effectively.
Malware Protection
Malware is one of the biggest and most common threats to network security.
It can infect computers and networks leading to damage to computer systems, malicious data encryption (ransomware), and data exfiltration.
Malware protection solutions are designed to detect and prevent malware from infecting your network via the most common vehicle for infiltration: the Internet.
While you can get infected through malicious USB keys and drives, the most common way is through a malicious website or downloading a malicious file from the Internet.
Malware protection guards against these threats by analyzing web traffic to identify and block malware.
This usually includes a number of techniques such as signature-based detection, behavior-based detection, and virtual code emulation, to identify and block malware.
Putting together a proper malware protection solution can prevent everything from known malware infections to zero-day exploits and advanced persistent threats (APTs).
Web Filtering
Web filtering is a security mechanism that blocks access to malicious websites and content.
This is a list-based solution that blocks known malicious websites, and it can also be used to prevent employees from venturing into problematic areas of the Internet that may violate company policies, break local laws, or simply be time-wasting distractions.
The focus, however, is to reduce the risk of employees accessing malicious websites and content, which can lead to malware infections, data breaches, and other forms of cyber threats.
Web Filtering can also reduce the workload for IT teams if they no longer have to deal with issues related to web usage.
Compliance
Although not directly part of network security, compliance is a key consideration when looking at tools and technologies to keep your network secure.
Many companies are responsible for maintaining records for their customers including private information such as health data, credit card data, addresses, and more.
Holding onto information like this as a necessary part of your business only increases the need for solid network security as the consequences of a breach are that much greater.
That’s why Zero Trust Network Access and other modern tools are so important.
Under a traditional perimeter-based approach hackers will have an easier time obtaining sensitive information after a successful breach.
Choosing the Right Solution
Now that we understand what tools you need, how do you choose the right network security solution for your organization?
First, you need to anticipate growth and increased demand for your network security needs.
Opt for solutions that can scale with your business, as well as offer the flexibility to adapt to new threats, and regulatory requirements. Quite often cloud-based platforms are the best choice when it comes to flexibility.
Cost is another important issue; network security investment isn’t just about upfront costs.
There can be many ongoing expenses, especially for hardware-based solutions that require regular maintenance, updates, and support.
And don’t forget about potential hidden costs such as additional licensing fees for certain features or upgrades after your initial service contract expires–it pays (literally) to do your due diligence to discover any potential hidden costs.
If your team is too small to allow for a full-time security expert then consider alternatives such as managed service providers (MSPs).
These specialized organizations offer a wide range of fully managed IT services. By outsourcing some or all of your network security functions to an MSP, your organization can benefit from the expertise and resources of a dedicated security team.
MSPs typically offer 24/7 monitoring and support, threat intelligence, and access to the latest security technologies, ensuring that your organization’s network is continuously protected.
Suppose you have pre-existing systems that cannot be replaced or are crucial for your business. In that case, you should also consider solutions that offer seamless compatibility with those systems.
Some common pre-existing hardware includes a data center firewall or possibly SD-Wan appliances.
By considering issues such as scalability, compliance, the total cost of ownership, and legacy integration, you can make an informed decision and select the most suitable network security solution for your organization.
Perimeter 81 Checks All the Boxes
Putting together all of these essential network security features and tools is easy with Perimeter 81.
This cloud-based, converged network security solution provides comprehensive network security focusing on ease of use, lightning-fast deployment, and easy scalability.
Most importantly, however, Perimeter 81 allows you to use ZTNA, Malware Protection, and Web Filtering from a single management console for easier all-around management.
If your ZTNA needs are simpler than most you can also use Perimeter 81’s Firewall as a Service to protect on-prem and cloud-based resources.
While you can permit access to all services to everyone in the company using the firewall, that is not recommended as granular access control is simple to implement with Perimeter 81 even for those with seemingly basic requirements.
A comprehensive network security strategy is critical for all organizations that want to protect their network and data from cyber threats.
This checklist allows organizations to build a robust and effective network security strategy that meets their specific needs and requirements.
Network Security Checklist – Download Free E-Book