The Web3 movement is going from strength to strength with every day that passes. Slowly but surely, it’s building a new iteration of the internet that promises to give power back to the people through the concept of decentralization and data ownership. Yet for all of its promises, Web3 has become an incredibly dangerous place to navigate, with the industry ceaselessly being targeted by cybercriminals, hackers and fraudsters.
The never-ending stream of Web3 security scandals hitting the headlines in the past couple of years has eroded much of the trust in the industry. In 2023, Web3 cyberattacks cost organizations and users more than $1.7 billion, according to a recent report by Chainalysis. The analysis highlighted 751 incidents involving Web3 projects that year, with the average cost of those incidents coming to $2.45 million. However, some of the attacks were far worse than others, with the top ten most damaging incidents accounting for $1.11 billion of the total losses.
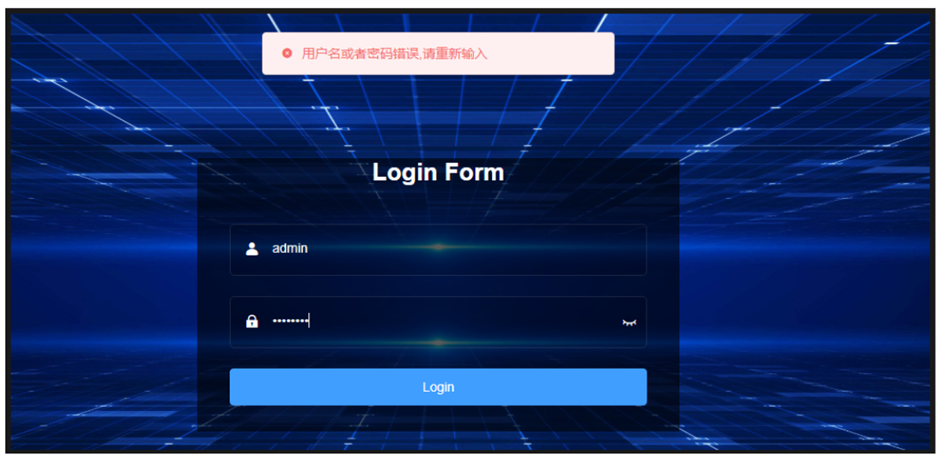
Web3 attacks come from multiple sources, with the 47 private key compromises identified being the most damaging, responsible for $880.9 million of the losses. Exit scams, phishing attacks and code vulnerabilities accounted for the rest of the industry’s losses.
Cybersecurity Has A Complexity Problem
If Web3 is to live up to its billing as the future of the internet, it’s going to need to win over the public’s trust, and the only way to do that is by countering the aforementioned threats. But one of the main challenges is that the cybersecurity industry is awash with thousands of different products and services, causing considerable confusion for companies as they struggle to determine which blend of products they should rely on.
With so many application monitoring services, observability tools, identity and access management solutions and firewall products around, companies have added numerous cybersecurity products to their arsenal, to the point where they’ve lost control. Their security is dependent on a mishmash of siloed tools that have no way to correlate with one another, leaving their defenses littered with holes. Although there’s a natural tendency to think that adding more defenses equates to stronger security, Web3 project leaders might do well to consider a more refined approach.
Simplifying Cybersecurity For The Web3 Era
Enter Resonance Security. This startup has created a powerful, full-spectrum cybersecurity platform that aggregates numerous tools and cybersecurity solutions, and combines them with automated security risk analysis to identify the most pressing vulnerabilities. Once that’s done, it then uses AI to suggest the best way to plug those gaps. By leveraging an AI concierge, Resonance can guide even novices through the necessary steps required to implement effective security.
Resonance is led by its founder and chief executive officer Charles Dray, an entrepreneur who was among the first to realize that Web3 security can only be achieved by marrying it with traditional Web2-based cybersecurity solutions and techniques.
Dray began his career in the traditional financial industry, where he spent time shoring up the defenses of major banks such as Citi, JPMorgan Chase and SMBC, only to pivot to the blockchain industry when he came to recognize the possibilities of decentralized finance and Web3. Having joined the Web3 security ecosystem, as one of the earliest Web3 security pioneers, he quickly recognized the urgent need for a more comprehensive solution.
Resonance has spent the last couple of years building such a solution, and it’s ready for prime time with the debut of V1 of its platform, following a successful, year-long beta phase. The central element of Resonance V1 is its automated security risk analysis tool that provides each organization with an overall security score via a simple, easy-to-understand dashboard. This dashboard serves as the nerve center of the customer’s security efforts, and the security score helps to pinpoint the most urgent vulnerabilities and prevent cyberattacks effortlessly. One of the main advantages of this approach is it means Resonance can be used by any individual to test their project’s cyberdefenses, even if they have no background or experience in security at all.
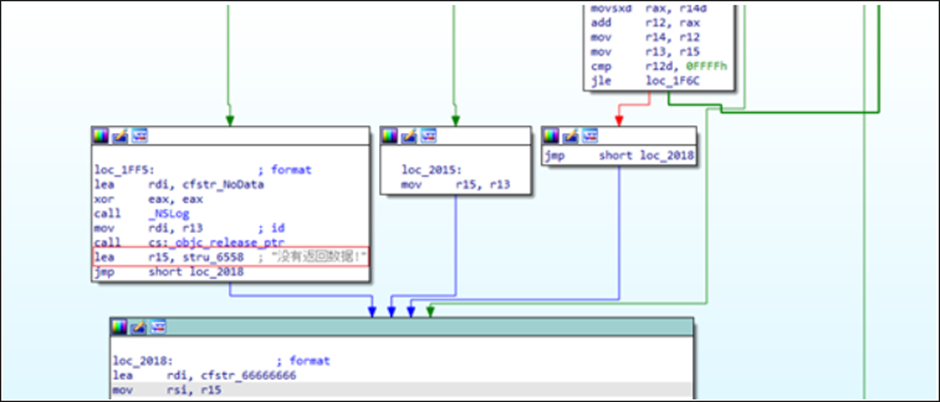
Identifying threats is the first order of business for Web3 security and Resonance provides the tools needed to do this extremely thoroughly. It’s a specialist in “offensive security”, with its engineers being among the best auditors in the business. Resonance provides blockchain and code audits that involve a detailed analysis of the underlying code used by Web3 platforms. In addition, its auditing services extend to smart contract code written in Cadence, Rust, Solidity and other common programming languages. These audits are crucial for any Web3 dApp to identify bugs and protect their users from vulnerabilities.
Don’t Forget Web2!
With the code audits out of the way, Resonance goes further and conducts penetration testing on behalf of its customers, searching for vulnerabilities in the Web2 stack that hosts their dApps. This marriage of Web2 and Web3 security is essential, because every dApp still relies on legacy technology, yet this is often overlooked by the majority of Web3 products, Dray revealed.
“It’s important to keep in mind that Web2 is the “foundation” of Web3, but many builders seem to forget this,” Dray told CPOMagazine. “But building Web3 on a weak foundation will inevitably spell trouble. It’s alarming, but many Web3 projects we have seen just get a smart contract audit and stop there, forgetting about the Web2 parts.”
Resonance’s penetration tests involve searching for bugs in the underlying infrastructure of both applications and browser extensions, as well as the cloud environments they’re hosted in.
When it comes to shoring up defenses, Resonance is equally thorough, providing a suite of CI/CD and cloud security tools that can be integrated into application development processes, with support for cloud platforms such as AWS, Microsoft Azure and Google Cloud. Its website also lists vetted cybersecurity products from third-parties that can easily be implemented by any user, regardless of their technical skills. Through this approach, the company is amplifying cybersecurity to protect its customers against any kind of threat, even if it hasn’t built its own solution.
Finally, Resonance complements these offerings with an extensive cybersecurity education program that allows its customers to expand their knowledge and awareness of the kinds of threats they need to deal with, as well as any new attack vectors that evolve over time.
Resonance says its security stack is the only platform Web3 projects will ever need to bolster their security, automating the entire process so project developers can focus on building out their services. It all starts with the security scan, which is complemented by audits and pen tests to identify the biggest security holes. Then the AI concierge takes over, prioritizing the most urgent vulnerabilities and recommending ways to fix them. The education is really just the icing on the cake.
Dray said his company’s primary goal is to make full-spectrum cybersecurity easy to implement through its patent-pending algorithm, which considers each customer’s technical level, budget, scope and timeframe, before creating a custom plan of action.
“Projects often lack the guidance to determine what they need to do, due to the overwhelming number of cybersecurity products and services and a lack of time,” Dray said. “They usually give up and focus on marketing and growth. We make it possible to continue to focus on that while still protecting against cyberthreats.”
A Unique Proposition
Although it’s still a new player on the Web3 cybersecurity scene, Resonance has already made a big impact, building up a loyal customer base during its beta phase. This initial success stems from its realization of how Web2 security issues contribute to many of the threats that impact Web3 projects.
“From the outset, Resonance demonstrated a deep understanding of the intricacies involved in securing Kado’s flows and technology stack,” said Kado.Money Chief Executive Emery Andrew. “Their team exhibited not only technical expertise but also a genuine commitment to addressing our unique security concerns.”
As the adoption of blockchain and Web3 technology accelerates, there is a pressing need for a specialized cybersecurity platform to address the numerous risks and dangers in the industry. Resonance’s unique selling proposition lies in its comprehensive risk analysis, its automated guidance, its powerful offensive and proactive security offerings, and its willingness to embrace partnerships.
By bundling these capabilities into a single, easy-to-use platform, Resonance seems set to play a leading role in securing the next version of the internet.