While navigation apps are incredibly helpful, their constant GPS usage and background processes can take a toll on your phone’s battery life. And let’s face it, battery life is super important, especially on the road. So, it’s definitely an upside for an app to be battery-sufficient.
- GPS usage: The core function of navigation apps relies on GPS, which consumes significant battery. Frequent location updates further drain the battery
- Screen brightness: A bright screen, especially during daytime navigation, contributes to battery drain
- Data usage: Apps that rely on live traffic updates or real-time rerouting require constant data connection, impacting battery life
- Background processes: Some apps keep background services running even when not actively used, draining battery
It’s a tough call to declare a single winner, given the array of phone models, usage habits, and app versions out there. While there’s no official data, user feedback, and real-world experience shed some light. Generally, some apps tend to be more battery-friendly than others. Out of Google Maps, Apple Maps, and Waze, here’s the lowdown from most battery drain to least:
- Waze: Renowned for its community-driven traffic updates, Waze’s constant background location updates for traffic data gathering and real-time rerouting can be a drain on your battery.
- Google Maps: Strikes a good balance between features and battery usage. It might use slightly less battery than Waze, particularly with features like live traffic turned off. However, frequent location updates and high-resolution maps can still eat up some juice.
- Apple Maps: Recent updates have amped up Apple Maps’ battery efficiency. User feedback suggests it might be the most battery-friendly option among the trio, especially on iPhones. This could be due to optimizations for Apple devices and potentially less aggressive background processes compared to Waze.
Mobile data usage: Apple or Google?

Every byte counts when you’re surfing on mobile data, and when it comes to its usage, actual consumption can differ based on factors like network speed, map details displayed, and features used (live traffic, rerouting). According to statistics, Apple Maps takes the lead in data usage, with an estimated consumption of 1.83 MB per 20 minutes.
- Apple Maps: 1.83 MB per 20 minutes
- Google Maps: 0.73 MB per 20 minutes
- Waze: 0.23 MB per 20 minutes
Google Maps, on the other hand, uses 0.73 MB. However, data usage can increase with features like live traffic turned on or using high-resolution satellite imagery. Interestingly, Waze, also owned by Google, uses the least amount at 0.23 MB per 20 minutes. This could be because Waze relies more on community-sourced traffic data, potentially reducing the need for extensive data download.
User interfaces: Beauty is in the eye of the scroller
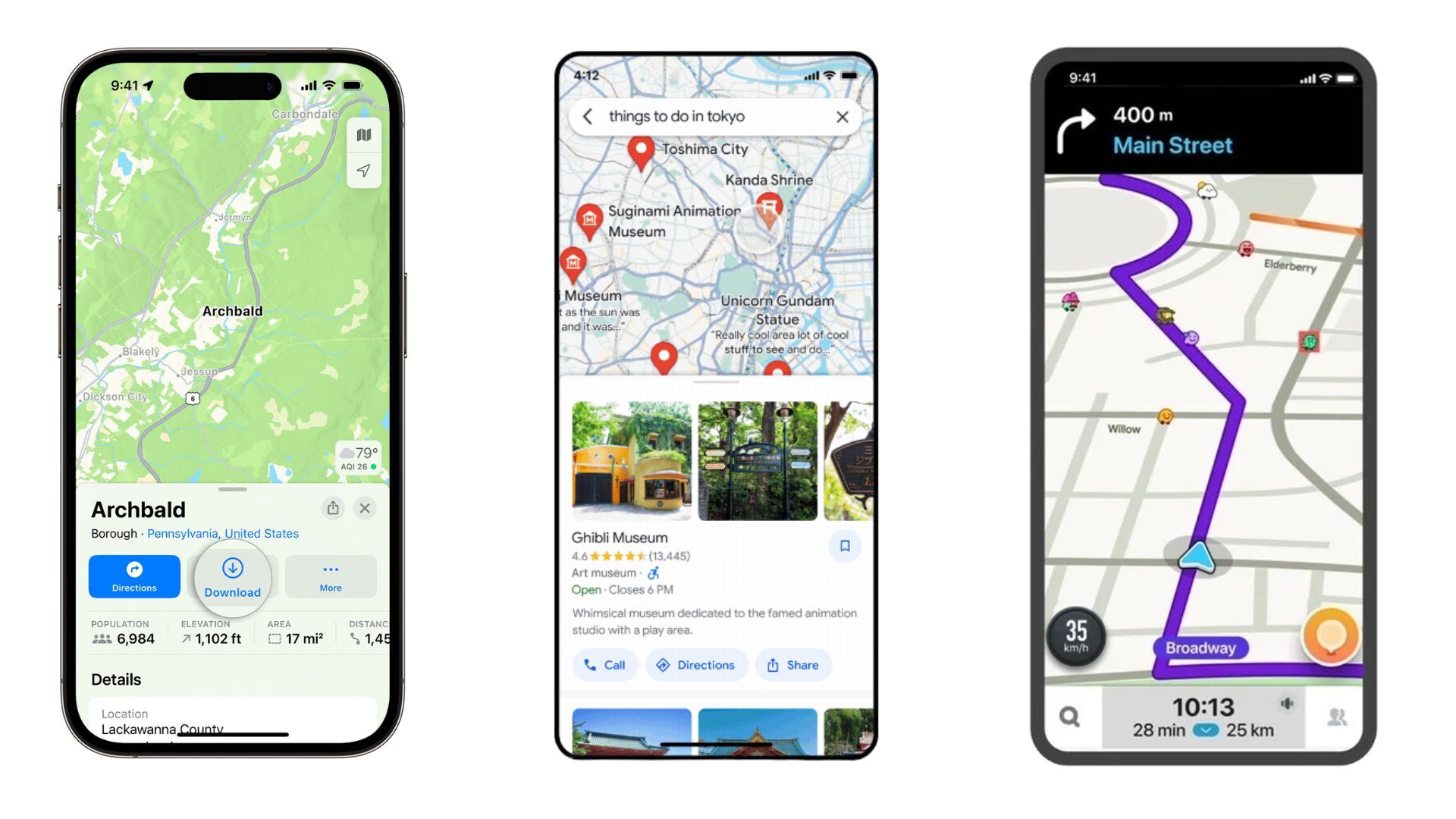
Apple Maps on the left, Google Maps in the center, Waze on the right
So, let’s talk about something more personal – the user interface. Comparing how the navigation apps look and feel can be a bit of a puzzle since we all have our own tastes. But hey, let’s see how they stack up against each other. First off, let’s check out the pros and cons of the Google Maps interface. If you have any other thoughts, feel free to drop them in the comments.
So, when it comes to Google Maps, there are a few things that come to mind:
Pros:
- It’s got a clean and familiar layout
- The map is big and easy to read
- The search bar is right there for quick destination searches
- And those traffic updates? They’re right on the map, super clear
- Sometimes, it feels like there’s too much stuff in the menu
- And the icons are kinda small, so you might need a few extra taps
Pros:
- It’s got that sleek, minimalist vibe that fits right in with iOS
- The map is nice and clean, no clutter
- Have you seen the 3D Flyover feature? Pretty cool stuff
- Plus, it’s got clear lane guidance for those tricky highway exits
Cons:
- You don’t have as much freedom to customize stuff compared to Google Maps
- And those point-of-interest icons? They could stand out a bit more
And, of course, we can’t forget about Waze:
- The interface is all vibrant and interactive and feels like you’re part of a community
- You get those real-time traffic updates and user-generated alerts front and center
- And big buttons make it easy to report stuff like hazards or police sightings
Cons:
- Sometimes it feels like there’s just too much going on, a bit overwhelming
- You might need a bit of time to figure out what all the buttons do
- And the map itself? It’s not always as clear as the others
So, in the end, it really comes down to personal preference. Try them all out and see which one clicks for you. Personally, I’ve got all three on my phone, not because I have to, but because I like to mix things up depending on what I need. But if I had to pick a favorite, it’s gotta be Google Maps, although I own an iPhone. It just gives me all the info I need, plain and simple.
Content and features: The Swiss army knife of apps
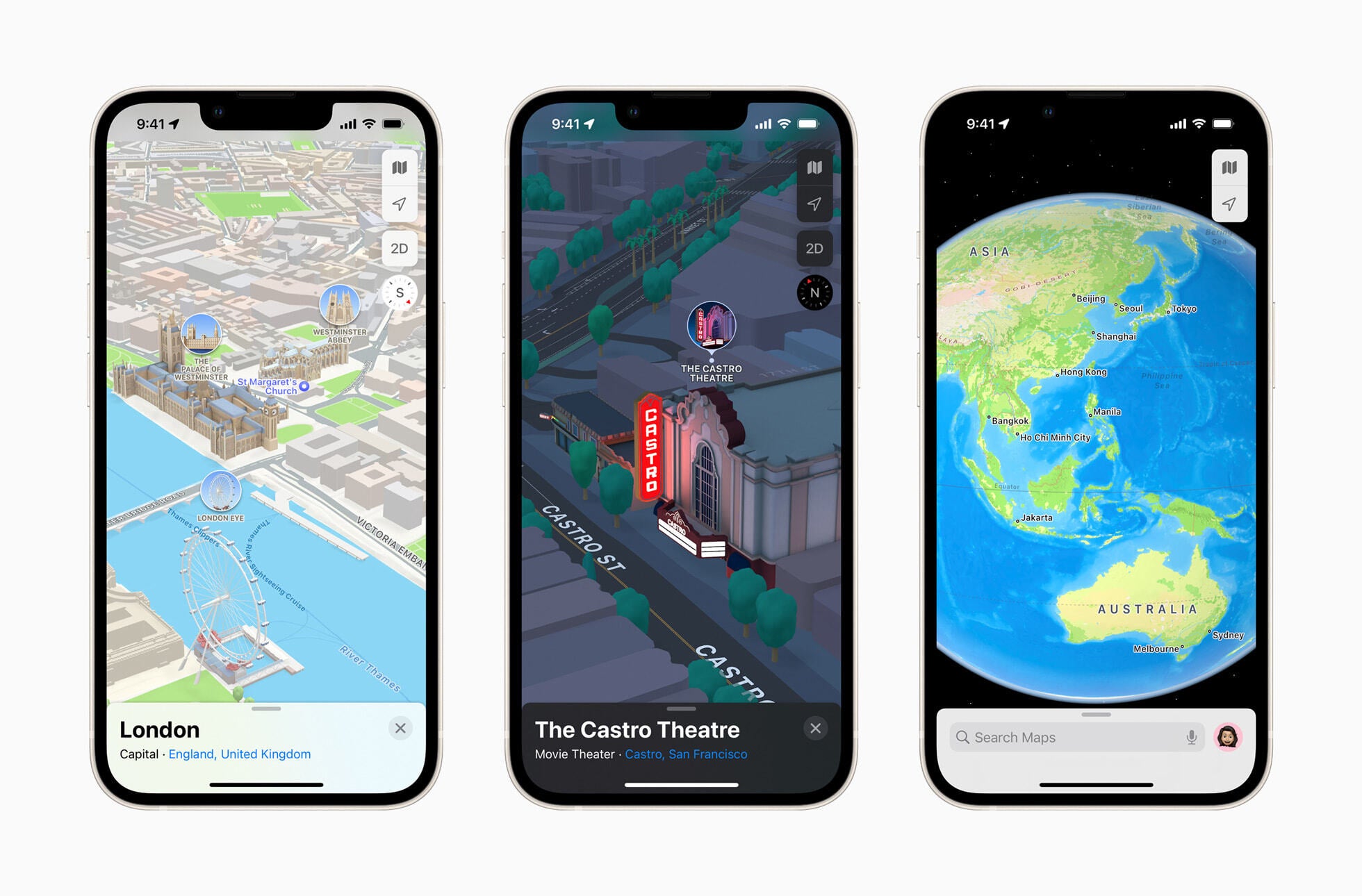
The 3D feature of Apple Maps (Image Credit–Apple)
When it comes to features and content about different points of interest (POIs), Google Maps is the real MVP. It’s packed with all the goods, like detailed reviews, ratings, photos, and even videos for some restaurants. Plus, you can book reservations or order food straight from the app.
Not long ago, Apple Maps stepped up its game with Apple Business Connect, offering similar info and letting businesses update their details. And guess what? iPhone users can now also order food or make reservations right from the card. Now, let’s check out some of the features of Apple Maps:
- Some cool 3D building visuals in select cities
- Turn-by-turn navigation with voice guidance
- Real-time traffic conditions with color-coded overlays
- Multi-stop routing for planning trips with multiple stops
- Look Around: A street-level view feature for exploring places virtually
- Lane guidance for tricky interchanges
- And hey, it’s all about user privacy – your data stays on your Apple device
Now, onto Google Maps:
- Everything from Apple Maps, plus more
- Detailed street maps, high-res satellite imagery, tons of POI info with reviews and pics, and 3D building visuals in many areas
- Live traffic updates with incident reports and ETAs
- Extensive public transit directions with real-time info
- Street View: Take a virtual stroll with panoramic street-level imagery
- Indoor maps for shopping malls, airports, and big buildings
- Offline maps for when you’re off the grid
- Google Assistant integration for voice commands while navigating
And last but not least, let’s take a look at Waze:
- Get real-time traffic updates straight from the Waze community
- Speed limit warnings and alerts for upcoming cameras
- Gas station price comparisons along your route
- Plus, earn points and badges for contributing reports
Offline navigation: Lost in the no-signal abyss?
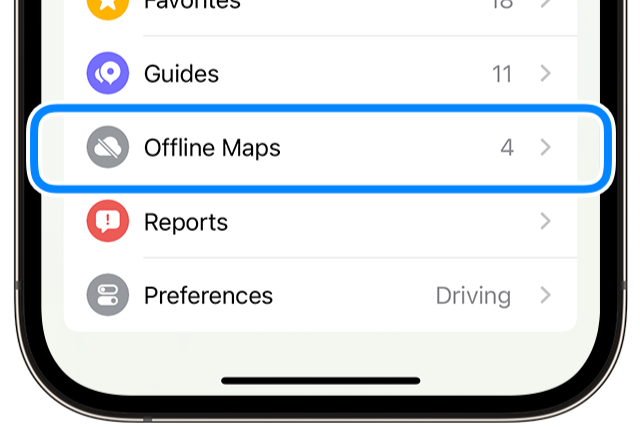
The Offline maps feature introduced with iOS 17 (Image Credit–Apple)
When you find yourself without a signal but still need to get to where you’re going, offline maps come to the rescue. Nowadays, not many folks are lugging around paper maps in their cars, so it’s handy that both Apple and Google Maps offer offline map options. With iOS 17, Apple jumped on board by introducing offline maps, allowing users to download maps for use when there’s no connection.
Google Maps has had this feature for a while, which is pretty nifty. It’s great to see both big players offering this option, as it can be a real lifesaver. However, Waze is a bit behind the curve in this department. While it’s got some cool features, like using real-time traffic conditions to find the quickest route, it still doesn’t offer a straightforward offline mode.
Here’s the deal with Waze: It relies on a data connection to do its magic. So, if you’re offline, you might hit a snag. But hey, if you’ve previously looked up info on your area of interest, Waze’s maps might still be available offline. So, it’s not a total bust, but it’s definitely something to keep in mind.
The final countdown: Google Maps, Apple Maps, or Waze?

Image Credit–Waze
When it comes down to choosing between Google Maps, Apple Maps, or Waze, it’s all about what works best for you. Personally (as I already mentioned), I’ve got all three on my iPhone, and I use them for different reasons. Google Maps is my trusty sidekick when I need valuable info about places and the most accurate routes in my neck of the woods. If I’m off the beaten path, Google Maps is my go-to.
Now, let’s talk about Waze. It’s got its perks, like keeping me informed about what’s happening on the road ahead. But sometimes, it takes me on routes that are… let’s just say, less than ideal, if they even exist, but that is a story for another time. It’s had its fair share of mishaps, but hey, it can still come in handy when you need to dodge a traffic jam or avoid a speeding ticket.
As for Apple Maps, it’s my go-to when I just need some background guidance. It’s there when I need it, simple and straightforward.
With so many navigation apps out there, you’re bound to find one that fits your needs like a glove. So, go ahead, explore your options, and find the one that suits you best.
[ad_2]
Source link