Android Automotive | Image credit — Google
Google is expanding the capabilities of its Android Automotive operating system to include messaging and VoIP apps, transforming cars into mobile communication hubs. This move is expected to enhance the driving experience for millions of Android users who rely on their cars for daily commutes and activities.This significant update to Android Automotive will introduce a new “Communications” category, encompassing both messaging and VoIP apps. An addition such as this means you’ll soon be able to stay connected with friends, family, and colleagues while on the road, all through the convenience of your car’s infotainment system and by using your messaging app of choice.Imagine being able to send and receive important messages without having to take your eyes off the road. The built-in voice assistant will read incoming messages aloud, allowing you to stay focused on driving while still staying in the loop. You can also send voice replies, keeping your hands on the wheel and your attention where it belongs. When your car is parked, you’ll have full access to the keyboard for more comprehensive messaging tasks.
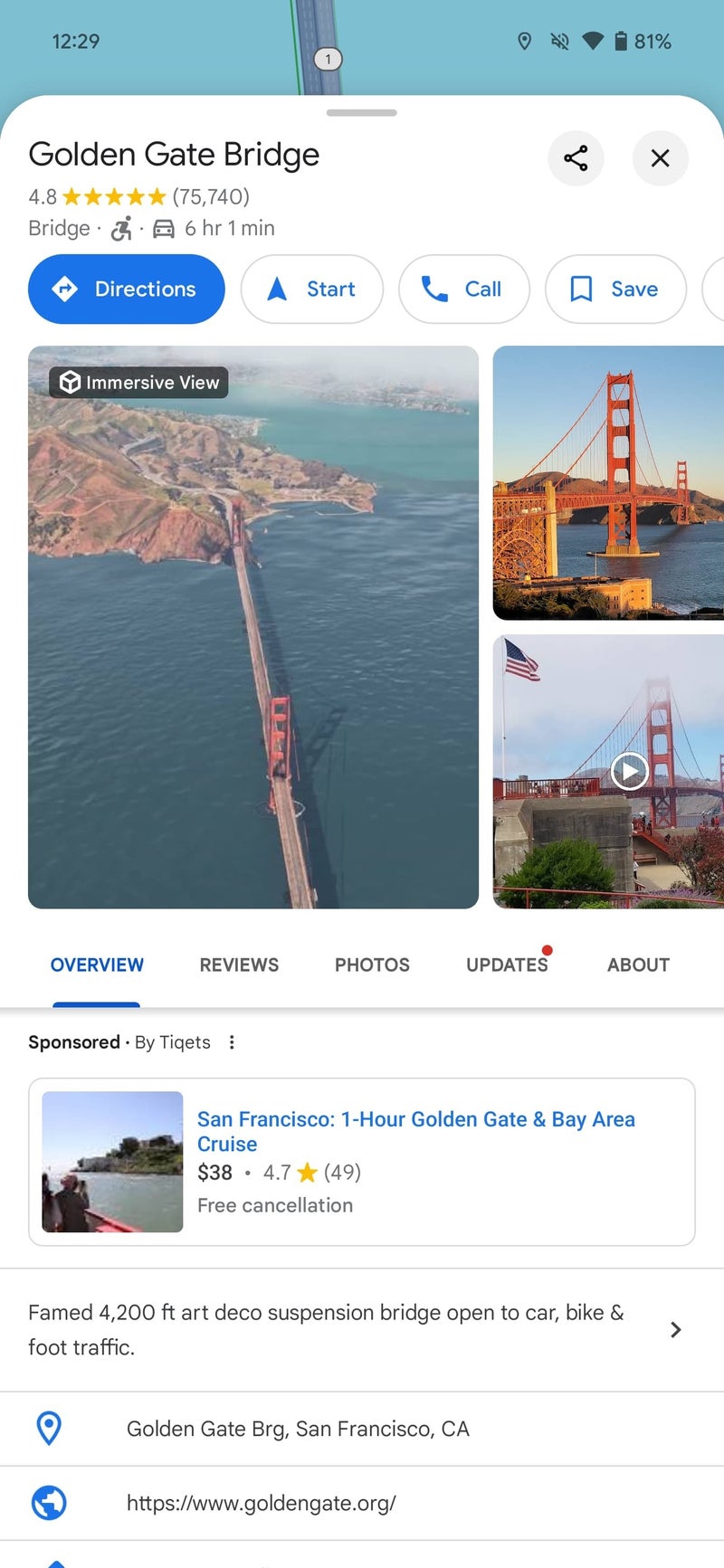
Google’s announced plans to expand support within Android Auto versus Android Automotive | Image credit — Mishaal Rahman (Android Authority)
But it doesn’t stop at messaging. Google is also opening the door to VoIP apps, enabling you to make and receive audio calls while driving. While video calls won’t be possible due to the lack of inward-facing cameras in most cars, the ability to participate in audio-only calls will be a game-changer for those who need to take important personal or work calls on the go. Some apps might even allow you to initiate or answer calls using just your voice, adding another layer of convenience and safety.It’s worth noting that messaging apps are already available on Android Auto, but with limited functionality. They primarily focus on reading messages aloud or sending voice replies. The addition of these apps to Android Automotive could potentially bring a wider range of features, making communication even more seamless and efficient.
While Google hasn’t released detailed documentation on how VoIP apps will function on Android Automotive, it’s likely that their interfaces will be streamlined for safety and ease of use. This is in line with the general approach of rendering most apps on Android Automotive using templates, ensuring a consistent look and feel across different apps. It remains to be seen how developers will address the challenge of rendering their messaging and VoIP apps on different vehicles, given the open-source nature of Android Automotive.[ad_2]
Source link



.webp)
.webp)
.webp)