The ShinyHunters hacker group claims the Ticketmaster breach is far bigger than previously anticipated, stealing 193 million barcodes, including 440,000 Taylor Swift tickets. Valued at $22 billion, they now demand $8 million from LiveNation!
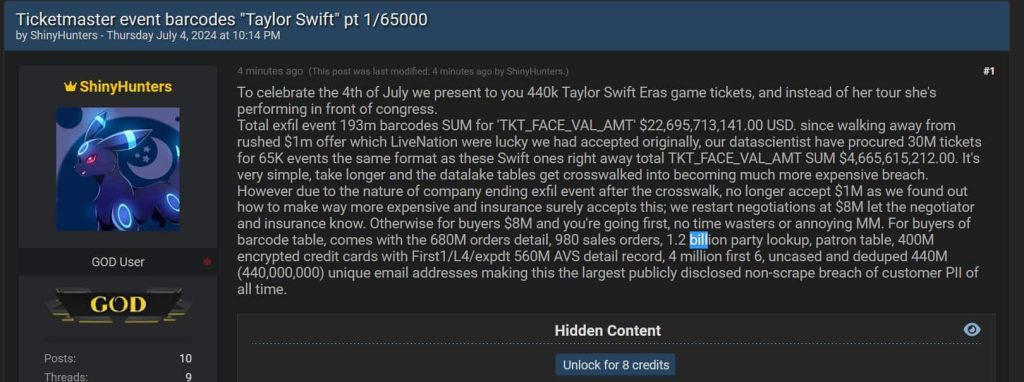
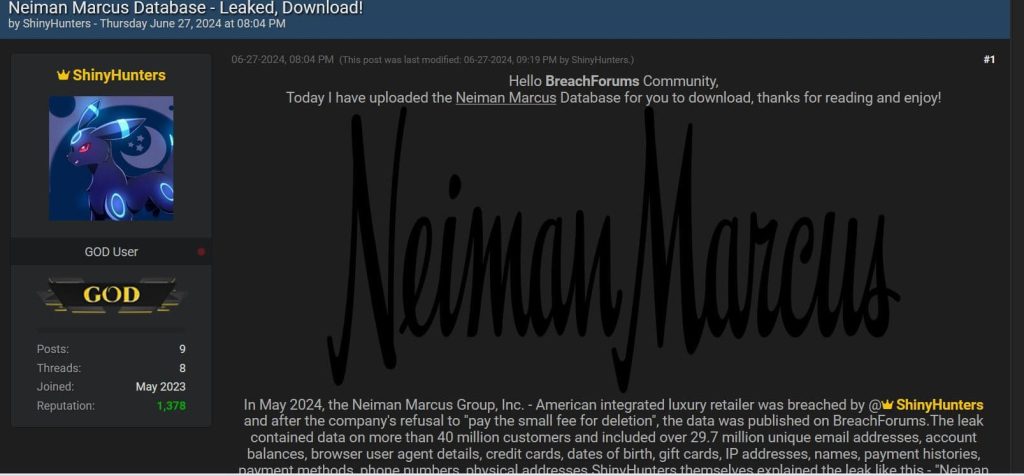
In May 2024, the notorious hacker group ShinyHunters breached Ticketmaster – LiveNation, as we know it. However, the hackers have now released new details about the extent of their breach. These details have been published on the infamous cybercrime and hacker platform Breach Forums titled “Ticketmaster event barcodes ‘Taylor Swift’ pt 1/65000.”
The Breach Unveiled
ShinyHunters marked the Fourth of July with a disturbing announcement: they claim to have stolen 440,000 tickets for Taylor Swift’s Eras Tour. In a symbolic twist, they suggest that instead of Swift performing on her tour, she will be “performing in front of Congress,” indicating this breach’s severity and public exposure.
The Staggering Numbers
The hackers provide an extensive breakdown of their hack:
- Total Exfiltrated Barcodes: 193 million
- Total Value of Stolen Tickets (TKT_FACE_VAL_AMT): $22,695,713,141.00 USD
A Shift in Negotiations
According to ShinyHunters, the hackers initially accepted a rushed $1 million offer from LiveNation to keep the breach under wraps. However, realizing the true value of the data they possess, they have escalated their demand to $8 million. They justify this increase by pointing out that they have found ways to make the breach more costly and complicated for the affected company.
Expanded Scope
In addition to the Taylor Swift tickets, ShinyHunters claims to have:
- 30 million tickets for 65,000 events: Similar to the Swift tickets, valued at $4,665,615,212.00 USD
Data at Risk
The hackers have detailed the extensive nature of the stolen data, which includes:
- 980 million sales orders
- 680 million orders detail
- 1.2 billion party lookup records
- 440 million unique email addresses
- 4 million uncased and deduped records
- 560 million AVS (Address Verification System) detail records
- 400 million encrypted credit card details with partial information
They boast that this breach is the largest publicly disclosed non-scrape breach of customer Personally Identifiable Information (PII) to date.
Disclosure:
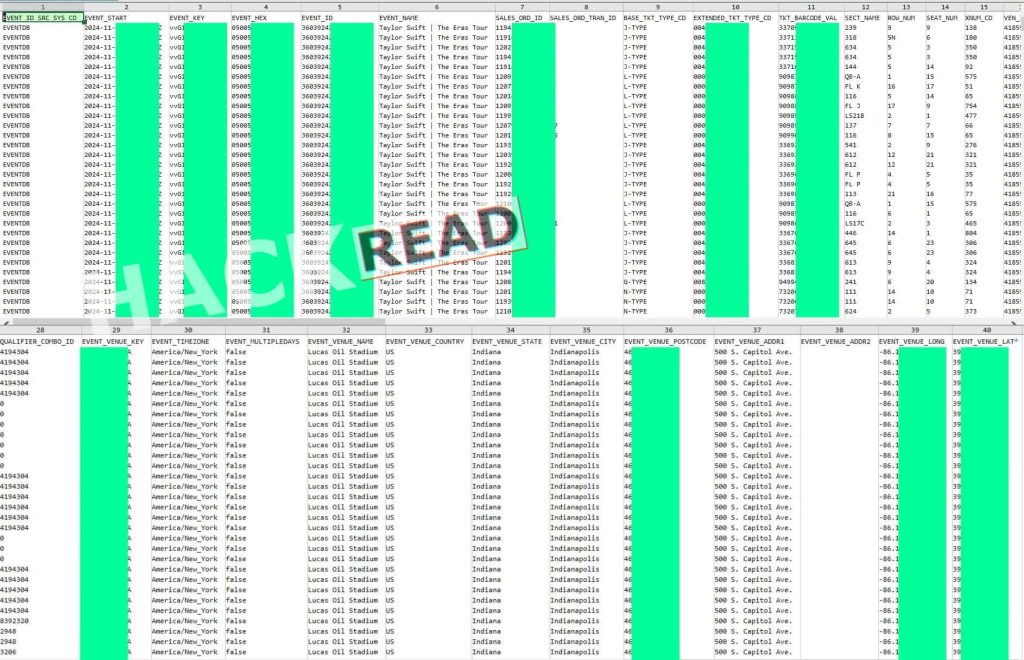
Hackread.com believes in transparency; therefore, we are publicly revealing that we used ChatGPT-4o to analyze the leaked data due to its complexity. Here’s the breakdown and conclusion:
The leaked data contains detailed information about ticket sales for Taylor Swift's Eras Tour event, specifically for a concert at Lucas Oil Stadium in Indianapolis, Indiana. Here is a breakdown of the key data fields present in the leak:Event Details:
EVENT_ID_SRC_SYS_CD: Source system code for the event.
EVENT_START: Date and time of the event.
EVENT_KEY: Unique identifier for the event.
EVENT_HEX: Hexadecimal representation of the event ID.
EVENT_ID: Numeric ID of the event.
EVENT_NAME: Name of the event (Taylor Swift | The Eras Tour).
EVENT_TIMEZONE: Timezone of the event.
EVENT_MULTIPLEDAYS: Indicator if the event spans multiple days.
EVENT_VENUE_NAME: Venue name.
EVENT_VENUE_COUNTRY: Country where the event is located.
EVENT_VENUE_STATE: State where the event is located.
EVENT_VENUE_CITY: City where the event is located.
EVENT_VENUE_POSTCODE: Postcode of the event venue.
EVENT_VENUE_ADDR1: Address line 1 of the venue.
EVENT_VENUE_ADDR2: Address line 2 of the venue (if applicable).
EVENT_VENUE_LONG: Longitude of the event venue.
EVENT_VENUE_LAT: Latitude of the event venue.
Ticket Details:SALES_ORD_ID: Sales order ID.
SALES_ORD_TRAN_ID: Transaction ID related to the sales order.
BASE_TKT_TYPE_CD: Base ticket type code.
EXTENDED_TKT_TYPE_CD: Extended ticket type code.
TKT_BARCODE_VAL: Barcode value for the ticket.
SECT_NAME: Section name where the seat is located.
ROW_NUM: Row number of the seat.
SEAT_NUM: Seat number.
XNUM_CD: Additional numerical code related to the seat.
VEN_ID: Venue ID.
HOST_SYS_CD: Host system code.
HOST_VAX_ACCT_NUM: Host VAX account number.
HOST_ACCT_CREATE_DT: Date when the host account was created.
TKT_FACE_VAL_AMT: Face value amount of the ticket.
TRAN_VOID_FLG: Indicator if the transaction was voided.
TRAN_VOID_DT: Date when the transaction was voided (if applicable).
CPN_CAT_ID: Coupon category ID.
CPN_PWD_PRIM_VAL: Primary value of the coupon password.
QUALIFIER_NAME1/2/3: Qualifier names.
QUALIFIER_COMBO_ID: Qualifier combo ID.
EVENT_VENUE_KEY: Venue key.Potential Uses of the Data
The barcode values (TKT_BARCODE_VAL) and seat details (section, row, seat numbers) can be used to create counterfeit tickets or resell tickets fraudulently.
Identity Theft and Financial Fraud:The data includes host account creation dates and VAX account numbers, which could be leveraged to identify and exploit user accounts.
Phishing and Social Engineering Attacks:With detailed personal information, attackers can craft convincing phishing emails or social engineering attacks targeting ticket buyers.
Market Analysis and Competitor Intelligence:Competitors can analyze the pricing (TKT_FACE_VAL_AMT), seating arrangements, and sales data to understand Ticketmaster's market strategies.
Reputation Damage:Public disclosure of this data can significantly harm Ticketmaster's reputation, causing loss of customer trust and future business.
The exposure of personally identifiable information (PII) might result in substantial fines from regulatory bodies and legal actions from affected customers.
Conclusion
The leaked data is highly sensitive and can be exploited in numerous malicious ways, from direct financial fraud to broader market implications and significant reputational damage for Ticketmaster. Immediate steps to mitigate these risks and protect affected customers are crucial.
Implications for Ticketmaster and Customers
This breach could have severe implications for Ticketmaster and its customers:
- Financial Loss: The face value of the stolen tickets alone amounts to billions of dollars. Additionally, the potential costs of managing the breach, compensating affected customers, and potential fines could be astronomical.
- Reputation Damage: Such a high-profile breach can severely damage Ticketmaster’s reputation, leading to loss of customer trust and future business.
- Customer Impact: The stolen data includes highly sensitive information, such as encrypted credit card details and personal email addresses, putting millions of customers at risk of identity theft and financial fraud.
- Increased Security Measures: This breach underscores the need for enhanced security measures within the company to prevent future incidents.
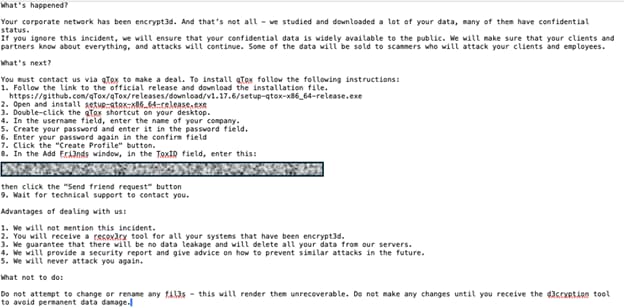
The ShinyHunters’ breach of Ticketmaster goes on to show the cybersecurity threat posed by cybercriminals. Although Ticketmaster previously acknowledged the breach, as the situation develops, it will be necessary for Ticketmaster to address the breach transparently, enhance its security protocols, and work towards restoring customer trust. Meanwhile, customers should remain alert and monitor their accounts for any suspicious activity.
For more updates on this developing story, stay tuned!
RELATED TOPICS
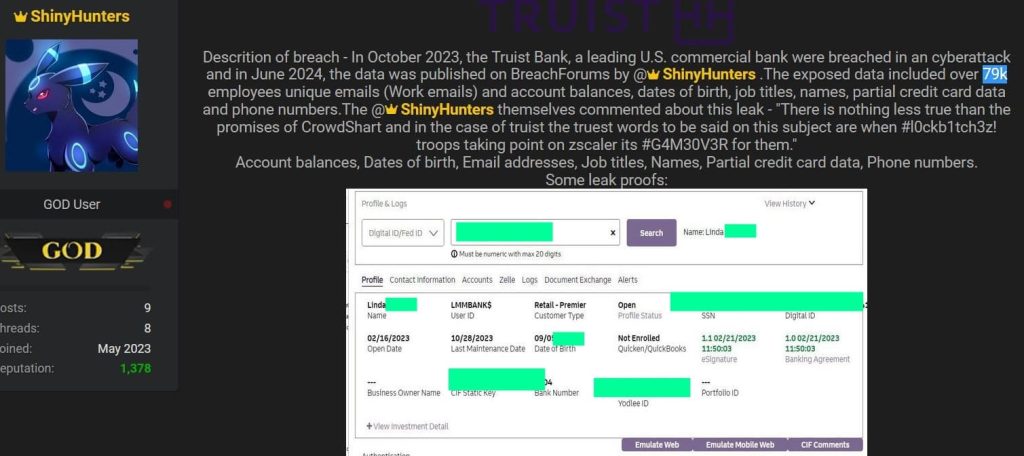
- BreachForums Returns Under ShinyHunters Hackers
- Alleged ShinyHunters Hacker Group Member Arrested
- TEG Ticket Vendor Breach: 30M User Records for Sale
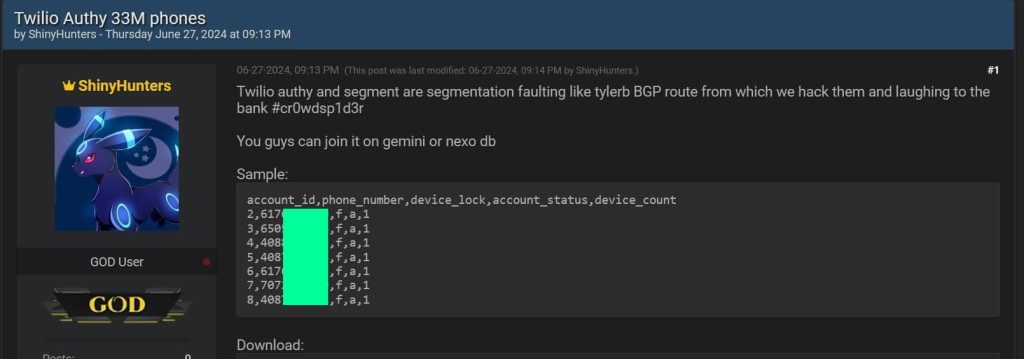
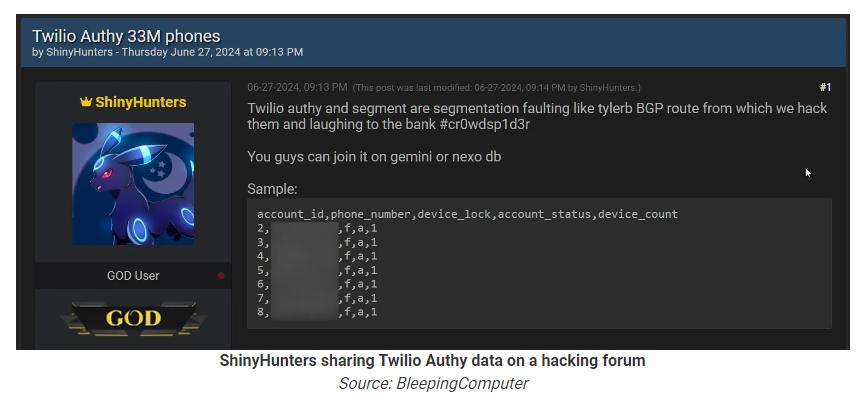
- ShinyHunters Leak 33 Million Twilio Authy Phone Numbers
- ShinyHunters Hacks Santander Bank: 30M User Data for Sale
- ShinyHunters leak database of Indian wedding site WedMeGood
- AT&T breach ShinyHunters selling AT&T database with 70M SSN
[ad_2]
Source link