Cybersecurity experts have identified a new type of malware called “Noodle RAT,” which Chinese-speaking hacker groups use to target Linux servers.
Although this malware has been active since 2016, it has only recently been properly classified, shedding light on its extensive use in both espionage and cybercrime.
The Emergence of Noodle RAT
Noodle RAT, also known as ANGRYREBEL or Nood RAT, is a backdoor malware with versions for both Windows (Win.NOODLERAT) and Linux (Linux.NOODLERAT).
According to the TrendMicro blog, Despite its long history, it was often misclassified as variants of other malware such as Gh0st RAT or Rekoobe.
However, recent investigations have confirmed that Noodle RAT is a distinct malware family.
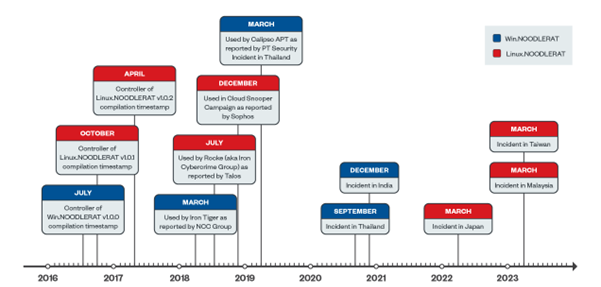
The timeline of Noodle RAT’s development and deployment is as follows:
- July 2016: v1.0.0 for Win.NOODLERAT compiled.
- December 2016: v1.0.1 for Linux.NOODLERAT compiled.
- April 2017: v1.0.1 for Linux.NOODLERAT updated.
Multiple reports have documented attacks involving Noodle RAT since 2018, but it was often misidentified as other malware families.
Analyze any MaliciousURL, Files & Emails & Configuration With ANY RUN : Start your Analysis
Notably, espionage campaigns using Noodle RAT have targeted countries such as Thailand, India, Japan, Malaysia, and Taiwan since 2020.
Technical Details of Noodle RAT
Win.NOODLERAT
Win.NOODLERAT is a shellcode-formed in-memory modular backdoor. Groups like Iron Tiger and Calypso APT have used it. Its capabilities include:
- Downloading and uploading files
- Running additional in-memory modules
- Working as a TCP proxy

The malware uses loaders like MULTIDROP and MICROLOAD for installation and employs complex encryption algorithms for C&C communication.
Linux.NOODLERAT
Linux.NOODLERAT, an ELF version of Noodle RAT, has been used by groups such as Rocke (Iron Cybercrime Group) and the Cloud Snooper Campaign. Its capabilities include:
- Reverse shell
- Downloading and uploading files
- Scheduling execution
- SOCKS tunnelling
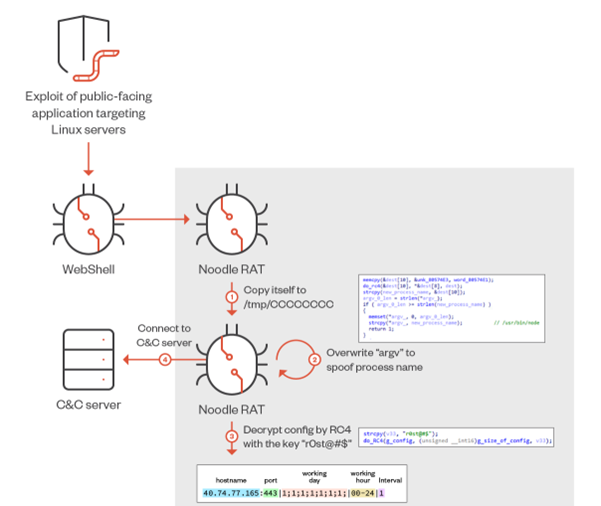
The malware is typically deployed as an additional payload of an exploit against public-facing applications and uses sophisticated encryption algorithms for C&C communication.
Backdoor Commands
Both Win.NOODLERAT and Linux.NOODLERAT implements various backdoor commands. The following table summarizes some of these commands:
| Actions | Type 0x03A2 (Win) | Type 0x132A (Win) | Type 0x03A2 (Linux) | Type 0x23F8 (Linux) |
| Successfully authorized | 0x03A2 | 0x132A | 0x03A2 | 0x23F8 |
| Upload a file to C&C server | 0x390A | 0x590A | 0x3 | 0x3 |
| List directories recursively | 0x390A | 0x590A | 0x3 | 0x3 |
| Download a file from C&C server | 0x390A | 0x590A | 0x3 | 0x3 |
| Initiate reverse shell session | N/A | N/A | 0x1 | 0x1 |
Similarities with Other Malware
Noodle RAT shares some similarities with Gh0st RAT and Rekoobe, but it is distinct enough to be classified as a new malware family.

For instance, while it uses some plugins from Gh0st RAT, the core backdoor code is different. Similarly, Linux.NOODLERAT shares some code with Rekoobe v2018, but the rest of its code is unique.
Recent findings have revealed control panels and builders for Noodle RAT, indicating a sophisticated malware ecosystem.
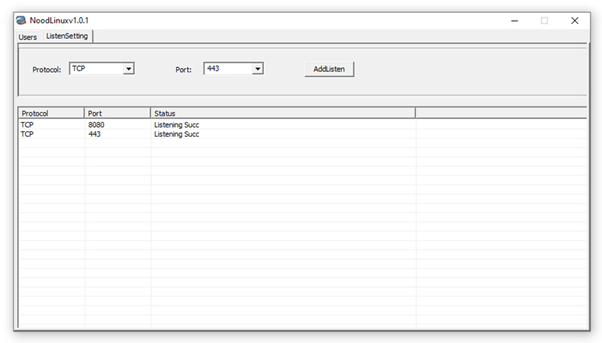
The control panel for Linux.NOODLERAT, named “NoodLinux v1.0.1,” supports TCP and HTTP for C&C protocol and requires a password to open.
Builders for Linux.NOODLERAT, versions v1.0.1 and v1.0.2, help create custom configurations for the malware.
Noodle RAT has been misclassified and underrated for years.
This new understanding of its capabilities and usage highlights the need for vigilance in cybersecurity, especially for Linux/Unix systems.
As exploitation against public-facing applications increases, Noodle RAT remains a potent tool for threat actors, making it essential for cybersecurity professionals to stay informed and prepared.
Looking for Full Data Breach Protection? Try Cynet's All-in-One Cybersecurity Platform for MSPs: Try Free Demo
[ad_2]
Source link


.webp)