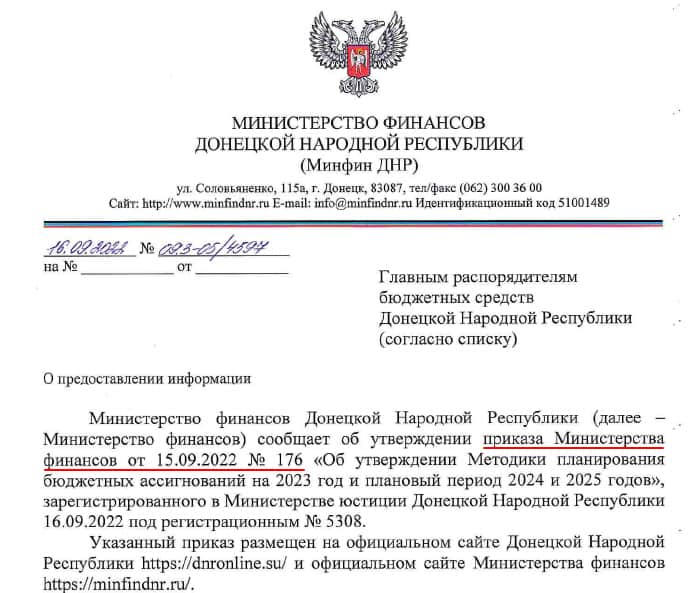
The primary targets of this phishing campaign are located in the Ukrainian regions of Crimea, Donetsk, and Lugansk, which were annexed by Russia in 2014.
Threat actors have launched a new spear phishing campaign in which they install a PowerShell-based PowerMagic backdoor and CommonMagic framework, according to a report by Kaspersky’s Global Research and Analysis Team.
The attackers send phishing emails containing malicious documents that lead to the installation of the backdoors. The primary targets of this campaign are located in the Ukrainian regions of Crimea, Donetsk, and Lugansk, which were annexed by Russia in 2014.
The emails are designed around the Russian-Ukrainian conflict, indicating that the attackers may have a specific interest in the regional geopolitical situation.
Kaspersky researcher Leonid Besverzhenko stated that the campaign is primarily an espionage operation targeting administrative, agricultural, and transportation organizations to steal sensitive data.
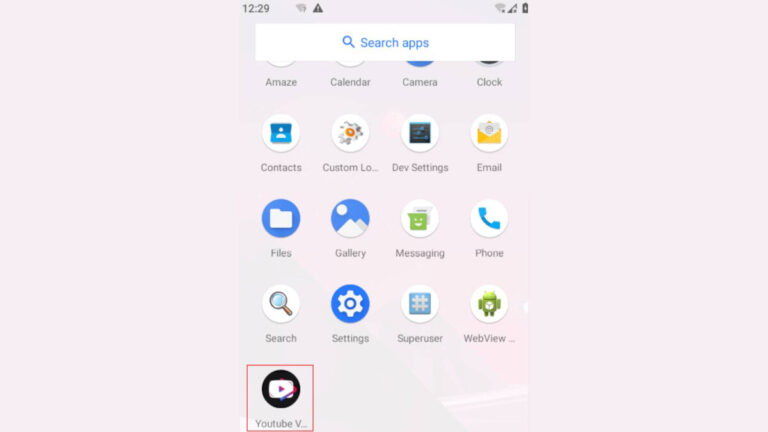
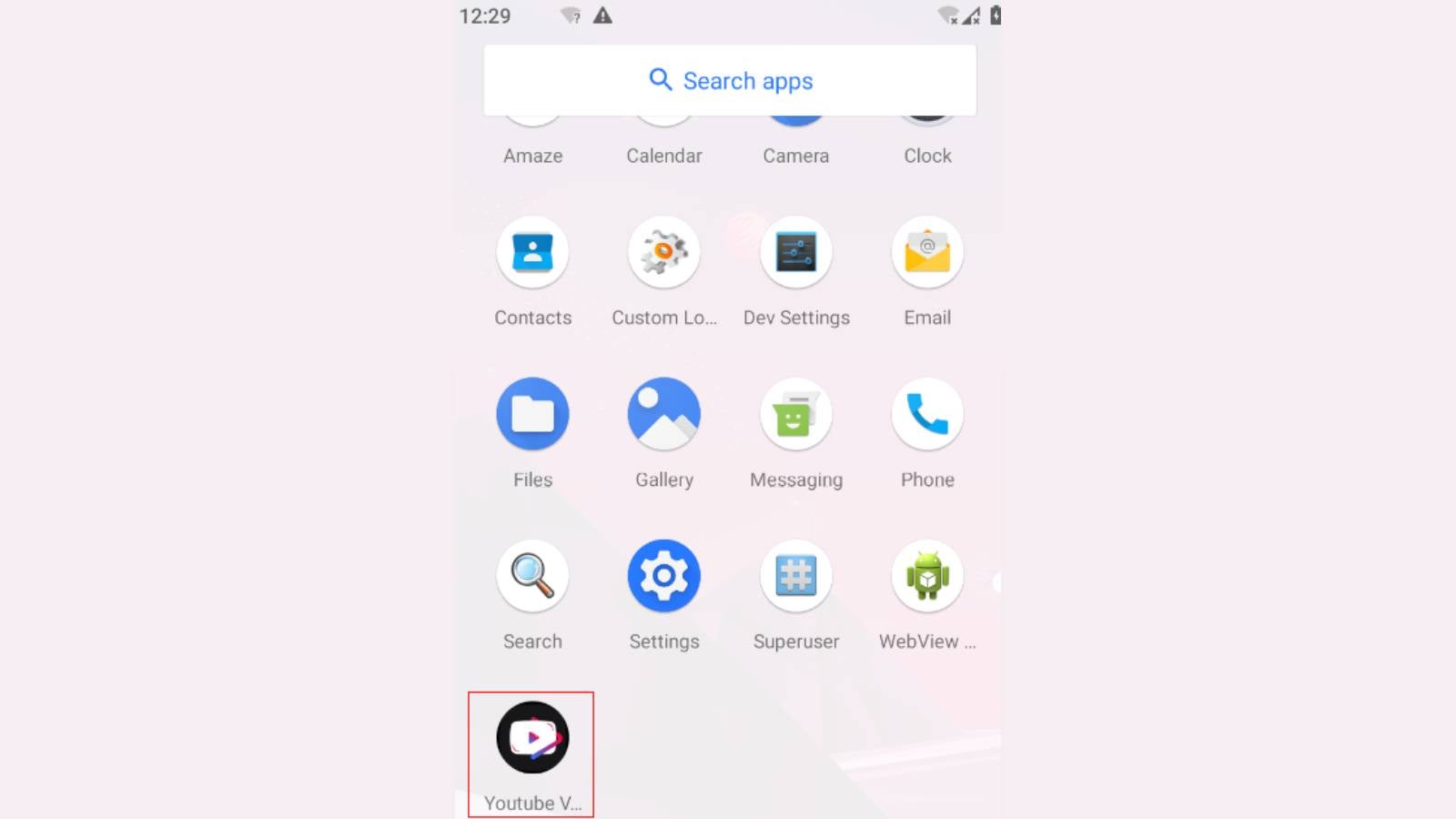
The phishing emails contain a URL that directs the victim to a ZIP archive containing a malicious LNK file disguised as a PDF. When the victim launches the file, their network is infiltrated, and PowerMagic establishes a connection with its C2 server using OneDrive and Dropbox folders, triggering infection through CommonMagic, a previously undiscovered “malicious framework.”
The CommonMagic framework includes separate modules for different tasks, such as encryption/decryption, screenshot capturing, and document stealing. It can also use plugins for stealing a wide range of files, including DOC, DOCX, XLS, XLSX, RTF, ODT, ODS, ZIP, RAR, TXT, and PDF from USB devices.
Additionally, it can take screenshots every three seconds by abusing the Windows Graphics Device Interface (GDI) API. Both malware have been in active use since September 2021, and Kaspersky discovered the campaign in October.
However, researchers have not yet been able to associate this campaign with a previously known actor. They do believe that an advanced threat actor is behind this campaign.
RELATED NEWS
[ad_2]
Source link







%20on%2051,000%20Websites.webp)







