The cybersecurity analysts at ESET recently reported that BlackLotus, a sneaky bootkit for UEFI (Unified Extensible Firmware Interface), has gained notoriety as the primary malware known to successfully evade Secure Boot defenses, creating it a formidable danger.
Even on the most current Windows 11 systems with UEFI Secure Boot activated, this bootkit has the capability to run seamlessly.
The implementation of UEFI bootkits in system firmware results in the provision of full control over the boot process of the operating system.
By exploiting this flaw, the operating system (OS)-level security mechanisms can be disabled and allow for the installation of arbitrary payloads with high privileges during the startup process.
Since October 2022, the UEFI bootkit has been available for purchase on hacking forums at a price of $5,000. Additionally, new versions of the bootkit are available at $200 each.
BlackLotus UEFI Bootkit
With a size of 80 kilobytes, this rugged and tenacious toolkit is programmed using Assembly and C. In addition, the program features geofencing capabilities to ensure that computers are not infected in the following places:-
- Armenia
- Belarus
- Kazakhstan
- Moldova
- Romania
- Russia
- Ukraine
In October 2022, information regarding BlackLotus was first brought to light. During this time, Sergey Lozhkin, a Kaspersky security researcher, referred to it as a complex crimeware solution.
In essence, BlackLotus leverages a security vulnerability known as CVE-2022-21894 (also referred to as Baton Drop) to bypass UEFI Secure Boot safeguards and establish persistence.
Following successful exploitation of this vulnerability, during the early boot stages, arbitrary code is executable. Subsequently, this enables a malicious actor to execute harmful actions on a system enabled with UEFI Secure Boot without the necessity of physical access.
To date, this is the initial instance of the publicized abuse of this vulnerability in a real-world environment. It is still possible to exploit it as the affected and legitimately signed binaries are yet to be included in the revocation list of UEFI.
BlackLotus exploits this by introducing its versions of legitimate binaries that are susceptible to vulnerability into the system to take advantage of the flaw.
BlackLotus is also designed to install a kernel driver and an HTTP downloader besides having some exceptional capabilities to deactivate security mechanisms such as:-
- BitLocker
- Hypervisor-protected Code Integrity (HVCI)
- Windows Defender
These components communicate with a command-and-control (C2) server to download additional malware in either:-
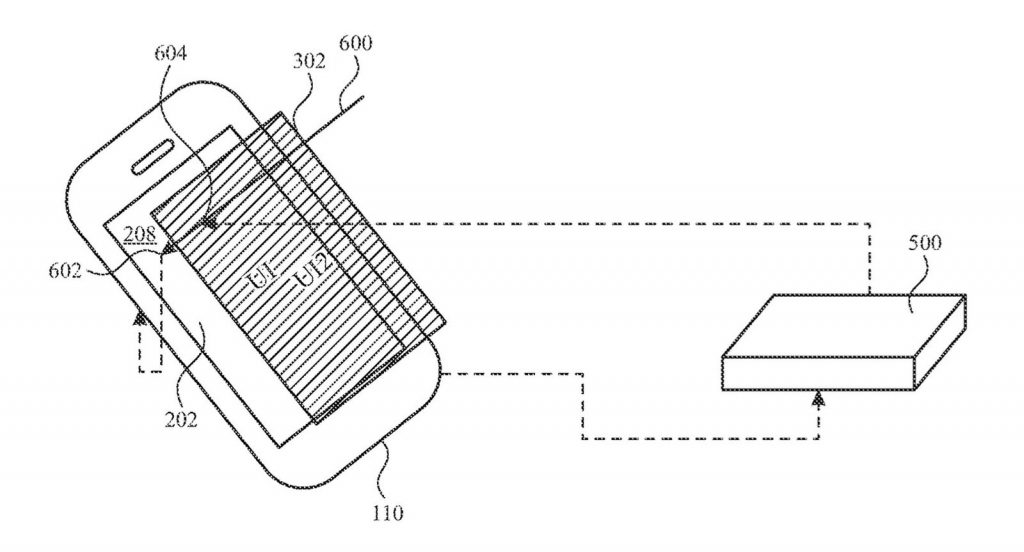
There is currently no clear understanding of the precise method used to implement the bootkit. However, it appears to commence with an installer component that takes on the responsibility of composing the files to the EFI system partition.
Following this, the installer component will disable HVCI and BitLocker, and subsequently initiate a reboot of the host. The attackers are also capable of exploiting CVE-2022-21894, exploiting it for persistence and installing the bootkit upon restarting the system.
There are a number of exploits that are implemented within this bootkit which allows the attacker to maintain control over the system by executing the kernel driver automatically upon the start-up of the system.
First, the kernel driver executes the HTTP downloader in user mode, and secondly, it executes the kernel-mode payloads in the second stage, which are all part of the next-stage HTTP download.
The actions performed by the malware are multifaceted and complex. These include downloading and executing various forms of malicious software, such as a kernel driver, DLL, or a standard executable.
Additionally, the malware has the ability to fetch bootkit updates and even uninstall the bootkit from the system that is infected.
Numerous critical vulnerabilities that have the potential to impact the security of UEFI systems have been identified in recent years.
However, due to the intricacies involved in the UEFI ecosystem and related supply-chain issues, many systems have remained vulnerable to these vulnerabilities long after they have been addressed, or at least after we have been informed of their resolution.
As computer systems with UEFI Secure Boot enabled have become increasingly common, it was inevitable that their vulnerabilities would be exploited by malicious actors.
Mitigations
Here below we have mentioned all the mitigations offered by the security analysts:-
- You should always keep your system, as well as its security product, up-to-date.
- Avoid the use of known vulnerable UEFI binaries by revoking them in the UEFI revocation database in order to bypass UEFI Secure Boot.
- One of the challenges with revoking widely used Windows UEFI binaries is the potential for rendering a large number of systems, recovery images, and backups unbootable. Given the significant impact of such revocation, it is understandable that the process can often be slow, as it requires careful consideration and planning to minimize disruption and ensure that users are not left without access to their systems.
- BlackLotus’ bootkit is installed over a revoked bootloader, so it can make the victim’s system inoperable if the applications are revoked. This can be remedied by reinstalling the operating system or by performing an ESP recovery.
- As the bootkit uses a legitimate shim with a custom MOK key for persistent storage, if the revocation of the certificate would occur after BlackLotus persistence is set, then the bootkit should remain functional. To mitigate this attack, for protection purposes, it would be best to reinstall Windows as soon as possible and to make sure the attackers’ enrolled MOK key is removed using the mokutil program.
Network Security Checklist – Download Free E-Book
[ad_2]
Source link