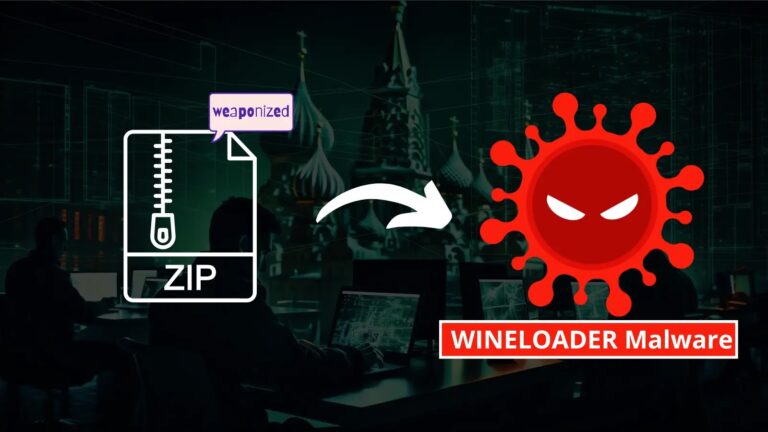
APT29, a Russian threat group, targeted German political parties with a new backdoor called WINELOADER using spear-phishing emails containing malicious links to ZIP files hosted on compromised websites.
The ZIP files deployed an HTA that initiated a multi-stage infection chain, delivering WINELOADER.
The backdoor has functionalities for communication with command and control servers and utilizes evasion techniques.
To defend against the APT29 campaign, security teams should understand these TTPs and the WINELOADER backdoor to improve detection capabilities.
APT29 uses spear-phishing emails with a malicious PDF attachment disguised as a wine-tasting invitation. The PDF tricks the victim into downloading a ZIP file containing an HTA (wine.hta or invite.hta).
.webp)
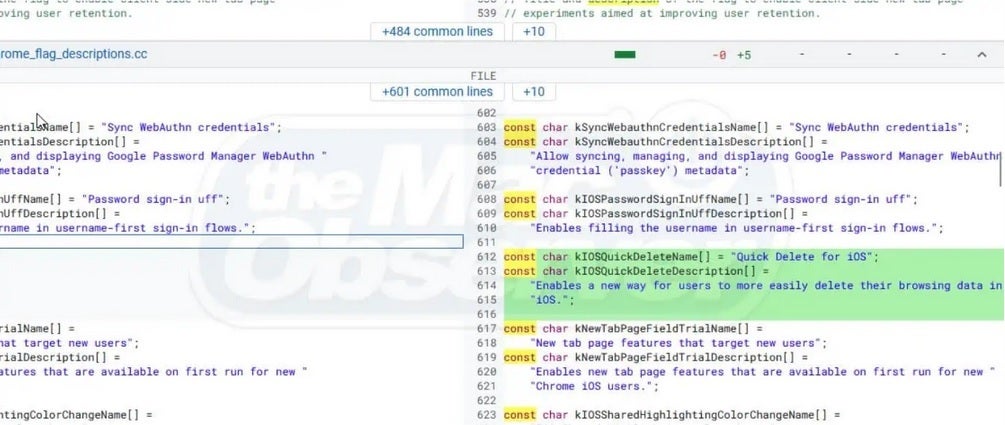
The HTA uses obfuscated JavaScript (potentially obfuscated with obfuscator.io) to download and execute a legitimate but vulnerable Microsoft binary (sqlwriter.exe or sqldumper.exe) along with a malicious DLL (vcruntime140.dll), which is side-loaded by the legitimate binary establishes the initial foothold for the WINELOADER infection.
Free Webinar | Mastering WAAP/WAF ROI Analysis | Book Your Spot
The Splunk Threat Research Team created an Atomic Red Team test to simulate the initial access of the WINELOADER campaign, excluding the data exfiltration tools, which involve an HTA triggering a base64 decoded payload (invite.zip) containing a DLL (gup.exe).
It mimics the side-loading behavior but uses a non-malicious DLL and to further emulate real-world attacks, the test injects sqlwriter.exe within a benign vcruntime140.dll.
Security teams can evaluate their capacity to identify these APT29 TTPs by running and analyzing this test, which will enable them to improve their analytics, response processes, and overall security posture.
.webp)
The HTA file exploits a DLL side-loading vulnerability. It first writes the Base64-encoded content of a malicious ZIP file (invite.zip) to a text file (invite.txt) on the system, then decodes the text file back to a ZIP and extracts its contents.
It triggers a user prompt, “Are You Ready?” before executing the payload, likely a malicious DLL named gup.exe and if the user clicks “OK,” the DLL is loaded and likely spawns calc.exe as a test.
A final message box confirms successful DLL side-loading with the Atomic logo.

WINELOADER exploits legitimate applications like SQLWriter.exe or Sqldumper.exe through DLL side-loading by loading a malicious vcruntime140.dll that triggers code execution.
The code decrypts a hidden data block using the RC4 algorithm with a key stored within the malicious DLL itself, allowing WINELOADER to gain initial functionality on a compromised system.
.webp)
Researchers analyzed a malicious DLL file (vcruntime140.dll) containing a variant of WINELOADER malware, which is encrypted with the RC4 algorithm and hides critical components like API names and strings to avoid detection
.webp)
After decryption, the malware connects to its command and control server (C2) and downloads additional malicious components.
The report provides the C2 server addresses and user-agent strings used by the malware.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAP.
[ad_2]
Source link



.webp)
.webp)



.webp)