WhatsApp is always working on some new feature to help enhance the experience, and this is why it’s one of the most popular messaging platforms on the web. According to a new report, WhatsApp is working on a new Notes feature for contacts. As it stands, it appears that this feature will be available on the web initially.
As with any feature currently in development, you will want to take this news with a grain of salt. This feature was discovered in the latest beta version of WhatsApp for the web. However, neither WhatsApp nor Meta officially announced it. So, there’s a chance that it could be changed or canceled at any moment.
WhatsApp is working on a new Notes feature for contacts
Sometimes, when you are contacting a person via WhatsApp, there’s additional information about them or your interactions that you want to keep track of. Well, according to a new report, WhatsApp is working on a way of doing so easily. Simply named Notes, this feature is currently being tested for the WhatsApp web version.
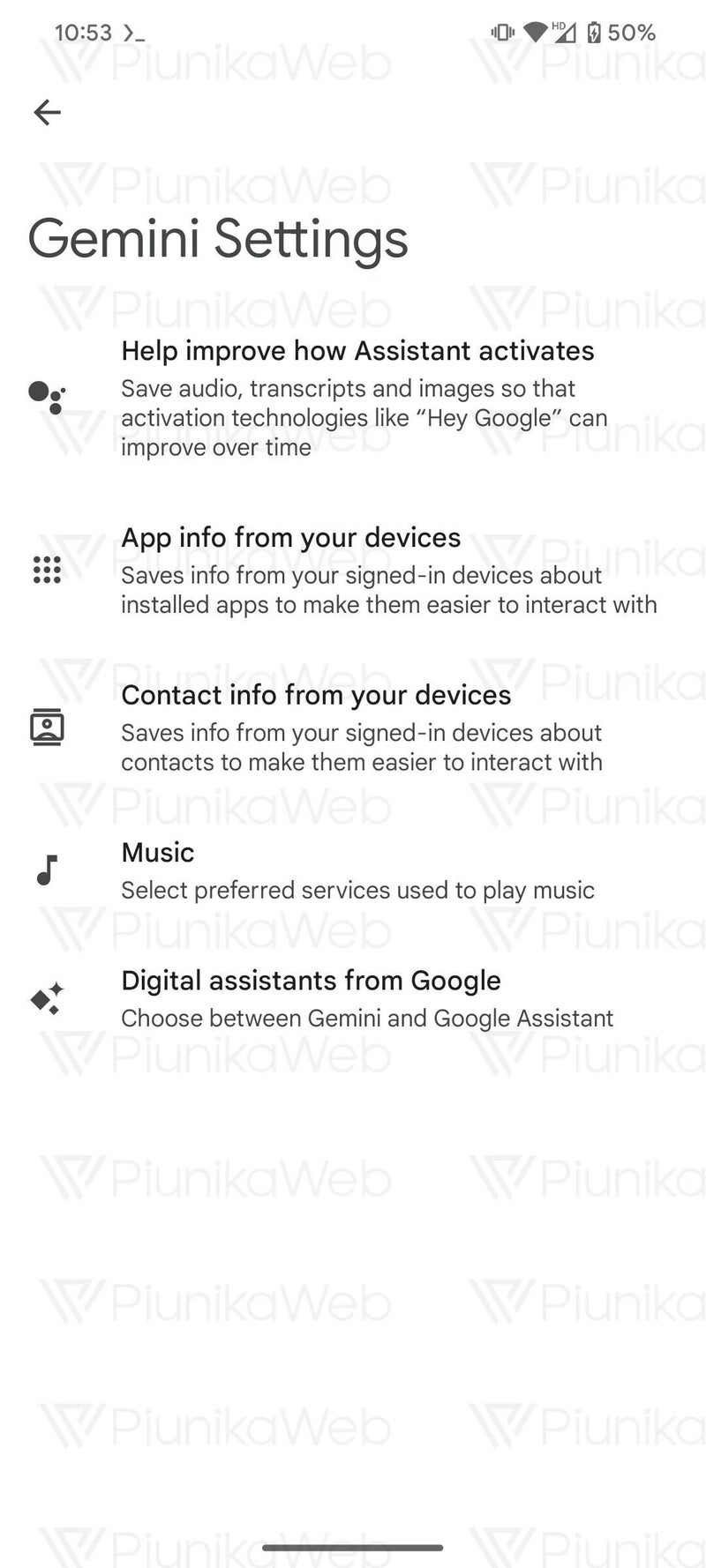
Looking at the screenshot below, we see a new text field in the contact info screen. One thing to note is that the account being used is a WhatsApp Business account. At this point, there’s no telling if this feature will be exclusive to business accounts or if it will be free for all.

In any case, you will be able to write down specific information about the contact. It could be the contact’s schedule, preferences, country of origin, language, Etc. You’re able to add notes about anything on the contact, and this could make it much easier to keep track of certain things to remember. If you are an avid WhatsApp user, and you have to keep track of a large number of contacts, then the Notes feature will be a notable lifestyle improvement.
At this point, there’s no word on whether or not this feature will make it to Android and iOS. However, it doesn’t seem likely that WhatsApp would keep this from the mobile market. It’s currently in development, so we should hopefully be hearing more about it soon.
[ad_2]
Source link