The Google Pixel 9 Pro XL is one of five Pixel flagships Google plans to announce this year. The Pixel 9 is also coming, as are the Pixel 9 Pro, Pixel 8a, and the Pixel Fold 2. The Pixel 9, Pixel 9 Pro, and Pixel 9 Pro XL are all expected to launch at the same time, in October this year. We have a separate Pixel 9 and Pixel 9 Pro preview articles, in case you’re interested in that. The ‘Pro’ models will be more powerful than the vanilla Pixel 9, though, of course.
At this point in time, we’re still quite some time away from the launch of the device. Therefore not a lot of information surfaced, but more is coming constantly. So we will keep updating the article, but for now, we’ll talk about what we know, and what we think we know about the device. So, let’s get to it, shall we?
This article will be regularly updated with new information on the Google Pixel 9 Pro XL (this is a preview article) — both official teasers and credible leaks, rumors, and insider claims — as it becomes available in the run-up to the release of the upcoming Android smartphone. This is the initial publishing of the article.
When will the Google Pixel 9 Pro XL be released?
The Google Pixel 9 Pro XL is expected to launch in October, alongside its siblings, the Pixel 9 and Pixel 9 Pro. The Pixel 7 series arrived on October 4, 2023, while the Pixel 8 series launched on October 6, 2023. Therefore, we do believe that the Pixel 9 series will also arrive in October. Well, unless Google has some major changes planned for this year. There’s a slight chance the event could take place in late September, we’ll see. We’re still months from the confirmation, though. Google likely won’t share the exact launch date until September.
What models are coming?
Last year, Google launched a single RAM variant of the Pixel 8 Pro, but that model arrived in several different storage options. The same is likely to happen this year. We probably won’t see more than one RAM variant of the Pixel 9 Pro XL. It’s very likely Google will stick with 12GB of RAM in the Pixel 9 Pro XL, but no info surfaced just yet, so it’s possible that will get upped to 16GB of RAM. It’s improbable, though. Google will use LPDDR5X RAM, though.
When it comes to storage, last year, the entry-level variant offered 128GB of storage. The same could end up being the case this year, though Google could up that to 256GB of storage. Chances are we’ll get several variants going up to 1TB of storage. Chances are Google will use UFS 4.0 flash storage this time around, while it used UFS 3.1 last year. The storage will not be expandable.
How much will the Google Pixel 9 Pro XL cost?
What about the Pixel 9 Pro XL price? Well, we still don’t have any information regarding that. The Pixel 8 Pro did start at $999 last year, and it would be preferable if Google kept that price tag intact, as the Pixel 9 Pro XL is its direct successor. There is a chance the company will bump it to $1,099, though, or something of the sort. The Pixel 8a is expected to get a price bump, so the same could happen with the Pixel 9 Pro XL. We are hoping that won’t be the case, though, as the $999 price tag would be most appealing to consumers.
What will the Google Pixel 9 Pro XL look like?
CAD-based Google Pixel 9 Pro XL renders did surface, so we have a good idea of what the phone will look like. Google will redesign the Pixel 9 Pro XL, to a degree. The device will have flat sides (all around), that are slightly curved toward the edges. That is a completely different approach to what the Pixel 8 Pro delivered. That’s not all, though. The phone will also include a flat display, unlike its predecessor. The display will feature very thin bezels, and those bezels will be uniform. A display camera hole will sit at the top of the display, and it will be centered.
We’ll also see a difference on the back of the device. The back side will be flat this time around. The camera visor will not be connecting to the left and right sides of the frame, as it did on the Pixel 8 Pro. It will be a separate pill-shaped entity on the back, though it will still be covered by metal. This approach is more similar to what the Pixel Fold delivered. The phone would look rather weird if Google went to connect that camera visor to the sides, now that both the sides and the back are flat.
It will have very similar measurements to its predecessor
The Pixel 9 Pro XL is said to measure approximately 162.7 x 76.6 x 8.5mm. So it will measure approximately the same as the Pixel 8 Pro. Along with the CAD renders, it was said that the display will be a bit smaller this time around. The Pixel 9 Pro XL is said to have a 6.5-inch panel, not a 6.7-inch one. That is highly unlikely, however. Considering that the size will remain unchanged, and the bezels either remain the same or be thinner, the display will either be a 6.7-inch or a 6.8-inch panel.
The Google Pixel 9 Pro XL will be made out of metal and glass, just like its predecessor. Its main speaker will be located at the bottom, along with a Type-C USB port. Three cameras will sit inside its camera island on the back. We still don’t know what to expect in terms of weight.
What specs will the Google Pixel 9 Pro XL have?
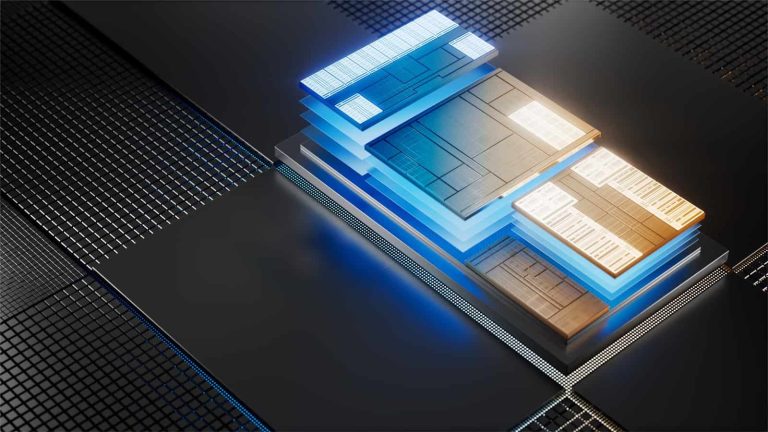
What about the phone’s specifications? Well, not a lot of information surfaced thus far, but we can try and guess what we’ll get. What we do know is that the Google Tensor G4 processor will fuel the phone. That chip will be made using Samsung’s 4LPP+ 4nm process. That is the same process as for the Exynos 2400, by the way. Google is expected to make a switch to TSMC with the Tensor G5 in 2025, as that will be a “fully-custom” chip. The Tensor G4 is expected to bring improvements to the table, though, of course.
A 6.5-inch display was tipped by @OnLeaks when CAD renders to shared. We believe that won’t be the case, though. The dimensions of the device will basically remain the same, and the display will remain flat. If we had to guess, we’d say the phone would include a 6.7-inch or a 6.8-inch panel. That will be a QHD+ LTPO AMOLED display, with an adaptive refresh rate of up to 120Hz. The panel is expected to be quite bright and support HDR10+ content too.
Google is expected to make a jump to UFS 4.0 flash storage
Google will most probably include 12GB of LPDDR5X RAM inside of the device. There’s a slight chance we may get 16GB of RAM instead, but that’s not as likely. It’s almost certain only one RAM variant will be available. We do expect multiple storage versions, however, likely going all the way up to 1TB. Google is expected to use UFS 4.0 flash storage this time around. The storage will not be expandable, by the way.
We’re not sure about the battery capacity just yet, but a unit of around 5,000mAh is expected. The Pixel 9 series is expected to support Qi2 charging standard for wireless charging, though. The company most likely won’t increase the speed of wired charging, so 30W charging is expected. Google could still surprise us, though. Do expect the phone to be IP68 certified for water and dust resistance too, and include a set of stereo speakers. We don’t have any information on the phone’s cameras just yet. We are, however, expecting main, ultrawide, and periscope telephoto units on the back.
Should you wait to buy the Google Pixel 9 Pro XL?
At the time of writing this article, the Pixel 9 Pro XL launch is over 6 months away. The Pixel 8 Pro is an excellent smartphone, and we get to see various deals for it quite often. If you do need a new phone, getting the Pixel 8 Pro as we speak may not be a bad idea. The Pixel 9 Pro XL is expected to be an improvement, for sure, but we do feel like the Pixel 10 Pro will be a much bigger jump. So if you do plan on upgrading after 1.5-2 years, getting the Pixel 8 Pro now, and then jumping to the Pixel 10 Pro may not be a bad idea. If you can wait, however, do wait a bit more, as more Pixel 9 Pro XL info is bound to surface in the coming weeks/months.





.webp)


.webp)