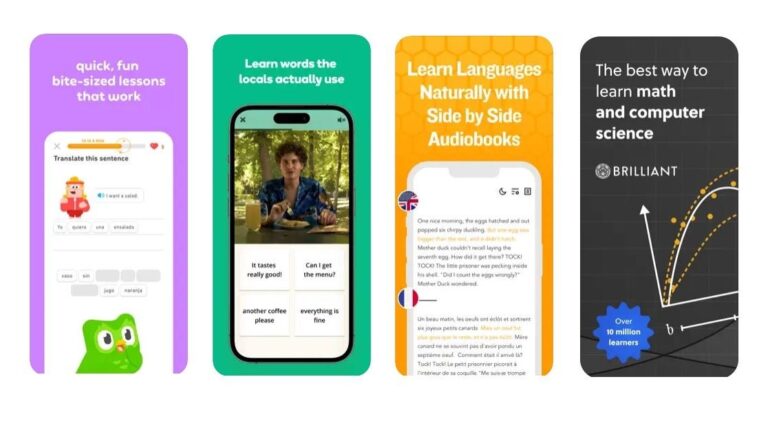
Duolingo is like having a language-learning buddy right in your pocket. This app lets you dive into learning a new language at your own pace, whenever and wherever you want. Imagine having a fun and interactive way to pick up Spanish, French, or any other language you’ve been itching to learn.Instead of boring textbooks or stuffy classrooms, Duolingo spices things up with games and challenges. You’ll tackle bite-sized lessons that feel more like playing than studying. It’s all about matching words, completing sentences, and even speaking out loud to practice your pronunciation.
You can choose from a bunch of different languages, from the super popular ones to the more niche ones, such as Japanese, Hebrew, and Arabic, which you might not find elsewhere. Plus, you can track your progress, earn rewards, and even compete with friends to keep things interesting. The basic version is free, but if you want to dig deep, there’s a subscription called Super Duolingo that offers an ad-free experience with the option to review your mistakes.
Memrise
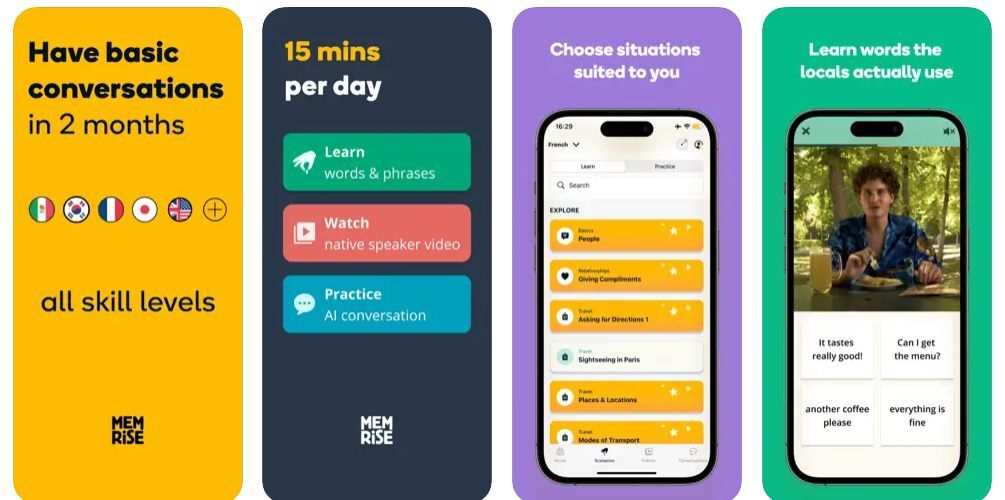
Price: Free with in-app purchases
Get Memrise for iOS here
Get Memrise for Android here
Memrise is another language-learning app that’s gained popularity for its unique approach to teaching languages. Similar to Duolingo, Memrise offers courses in various languages, but it stands out with its focus on vocabulary acquisition through mnemonic techniques.The app utilizes spaced repetition and mnemonic devices to help users remember words and phrases more effectively. Mnemonics are memory aids, like visual imagery or associations with familiar words, that make it easier to recall new vocabulary. Memrise incorporates these techniques into its lessons, making language learning more engaging and memorable.
Memrise also offers features like interactive games, listening exercises, and pronunciation practice to enhance the learning process. Like Duolingo, it’s designed to be convenient and accessible, allowing users to learn at their own pace, anytime and anywhere.
LingoDeer

LingoDeer is yet another language-learning app that offers interactive lessons in various languages, but primarily focusing on Asian languages such as Japanese, Korean, Chinese, and Vietnamese.
What sets LingoDeer apart is its structured approach to language learning, which is tailored specifically to the grammar and vocabulary of each language it teaches. The app provides step-by-step lessons that cover essential language skills, including reading, writing, listening, and speaking.
One of the key features of LingoDeer is its clear explanations of grammar points and language concepts, which are presented in a way that’s easy to understand and remember. The app also incorporates a variety of interactive exercises and quizzes to reinforce learning and help users practice what they’ve learned.The basic version is free, but you can buy different tiers of premium access, starting from a monthly subscription for $14.99 and going all the way up to a lifetime membership for $299 (often slashed down to $159.99).
Babbel
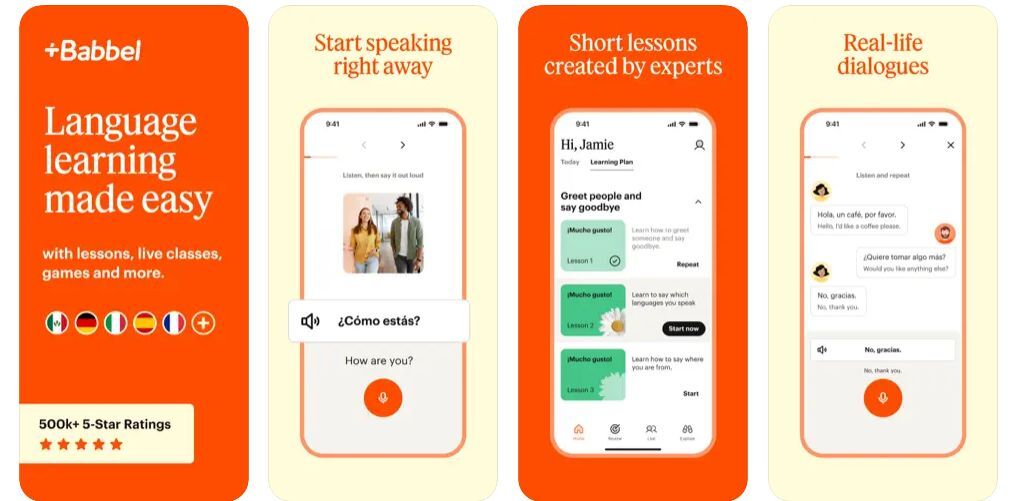
Babbel is one of the oldest language-learning tools on the internet, and it takes its name from the Babbel fish in the popular science-fiction book “The Hitchhiker’s Guide to the Galaxy.” The app does what other similar apps do but focuses more on the practical side of things, teaching you language skills that you can use in real-life situations.
That’s not to say that Babbel doesn’t offer a complete set of language learning tools, such as vocabulary, grammar, pronunciation, and cultural insights. It’s just that if you need to learn a couple of useful phrases for an upcoming short trip abroad, Babbel might be the right one for you.
Babbel also utilizes speech recognition technology to help you practice your pronunciation and ensure you’re speaking accurately, so you don’t make locals laugh on that upcoming trip. Plus, the app’s personalized review feature helps reinforce what you’ve learned, so it sticks with you for the long term.Just like the other apps on that list, Babbel is free with some in-app purchases and subscriptions, starting at $8.99/mo.
Beelinguapp
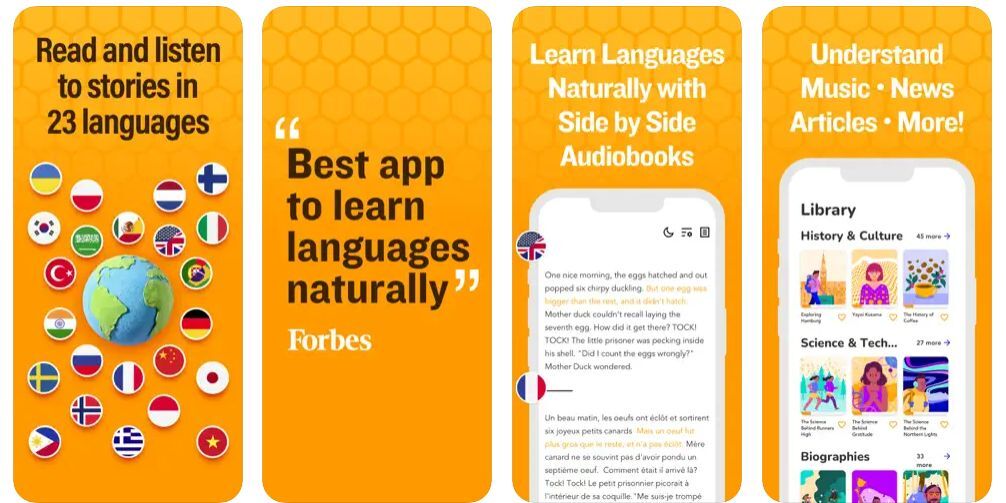
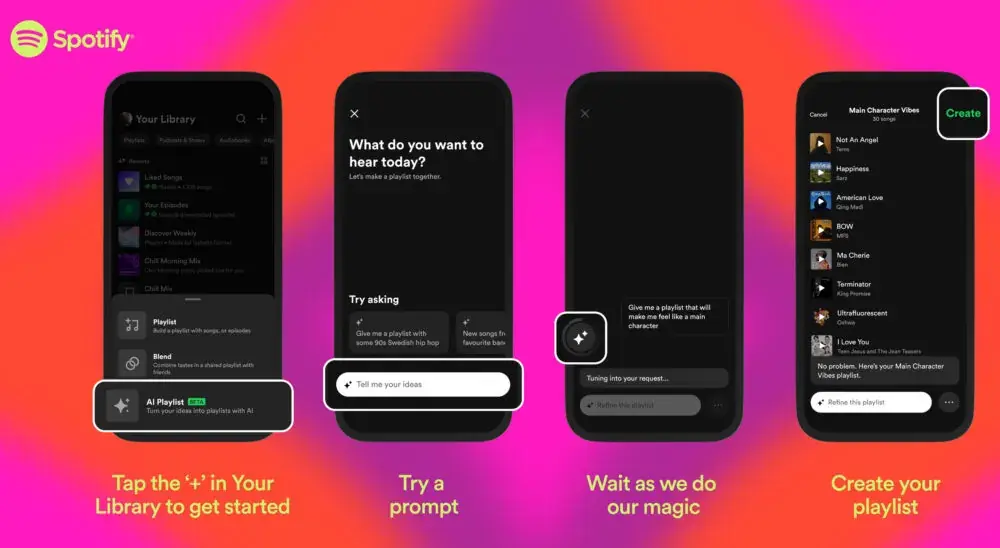
Tired of the same repetitive language learning apps that use gamification and other similar techniques to make you come back and do your lessons? Prepare for something completely different! Beelinguapp is a unique language-learning app that offers an innovative approach to learning languages through reading. Imagine Beelinguapp as your cozy reading nook, where you can dive into captivating stories and articles while effortlessly picking up a new language.
Here’s the magic: Beelinguapp lets you choose from a library of texts in different languages, so you can find something that piques your interest, whether it’s a thrilling story or a fascinating article. You get to read these texts side by side, with the original language on one side and a translation in your native language on the other.
Additionally, Beelinguapp offers audio recordings of the texts, allowing users to listen to native speakers read the text aloud. This feature helps improve pronunciation and listening comprehension skills. It’s one of the more organic ways of learning a language, and for some people, it might work better than puzzles, games, and achievements.Bonus: Brilliant
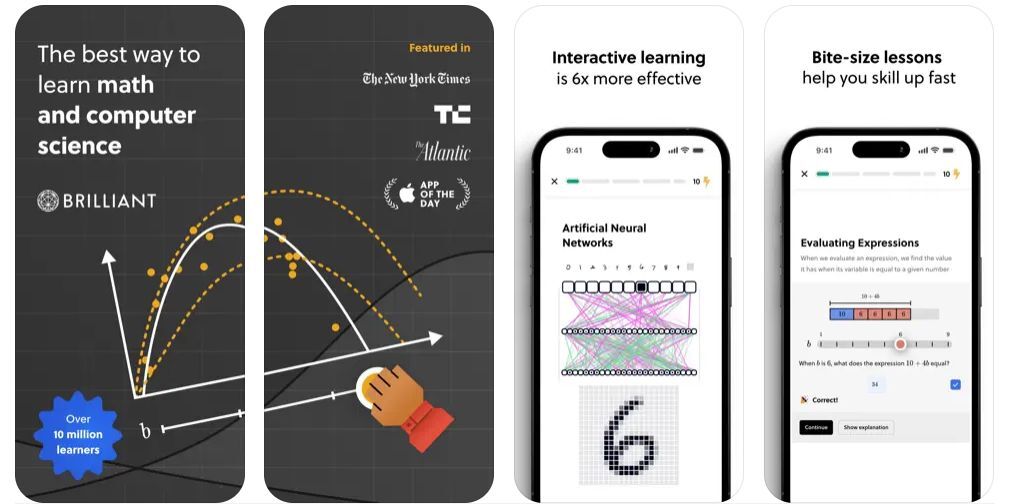
Learning a language is fun and all, but what about learning something different? How about delving into the deep and complex world of quantum physics or mathematics if you feel up for the challenge? There’s no need to go back to Uni and start a major in astronomy. There’s an app for that, and it’s called Brilliant.
Actually, Brilliant is a whole learning platform with a strong focus on math, science, and computer science, but before you click away, this platform is designed to explain complex subjects as intuitively as possible. It also provides learning at different levels, starting with beginner and going all the way up to expert, and it also features a range of interactive puzzles, quizzes, and challenges that encourage users to think creatively and apply their knowledge to real-world scenarios.
The downside is that the app requires a subscription. There’s a trial version that offers a glimpse at what you might achieve with the Problems of the Week feature, but if you want to get access to all the courses at a deeper level, you need to get Brilliant Premium.[ad_2]
Source link