Netcraft Report Uncovers “Darcula” Platform Targeting Postal Services Worldwide via iMessage & RCS Phishing. Discover how USPS & global services are under attack and learn essential protection measures.
A new report by cybersecurity firm Netcraft has discovered a sophisticated phishing-as-a-service (PhaaS) platform called “Darcula.” This platform is being used to launch large-scale smishing attacks targeting the United States Postal Service (USPS) and global postal services across more than 100 countries.
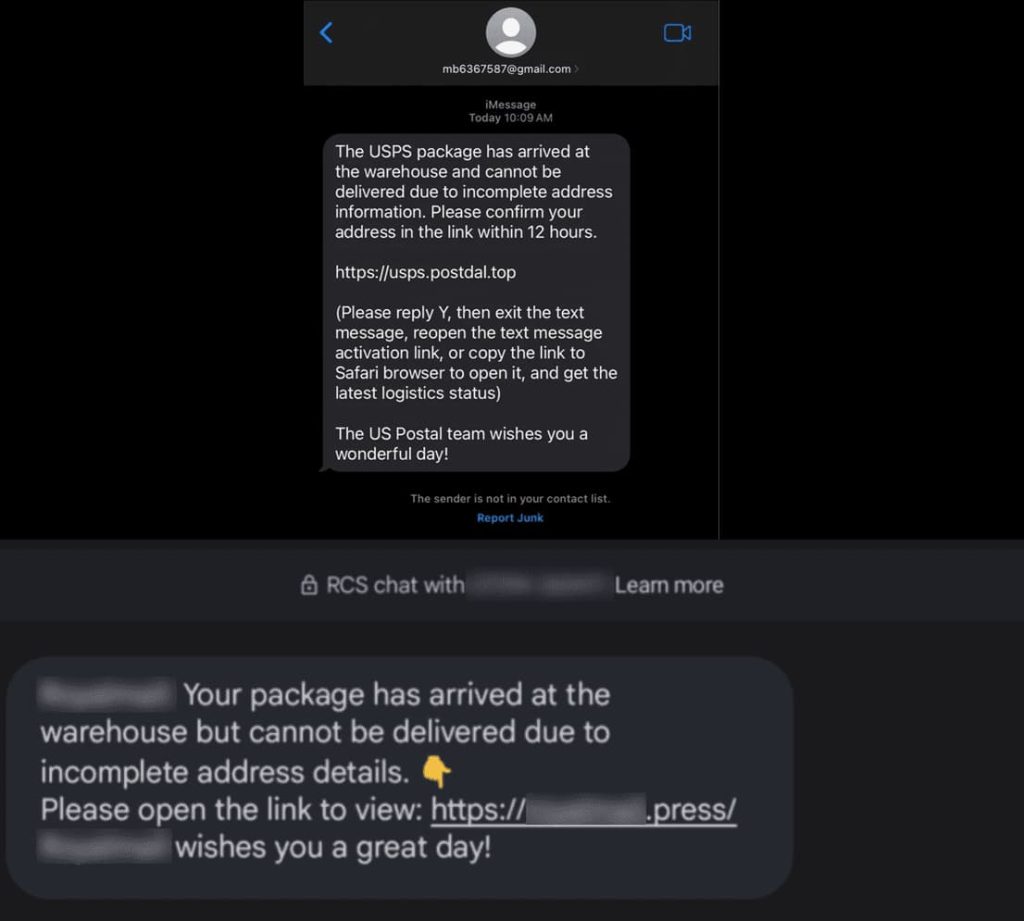
Darcula represents a significant development in the world of cybercrime. Unlike traditional PhaaS platforms that rely on email communication, Darcula leverages iMessage and Rich Communication Services (RCS) messaging for its attacks. This allows cybercriminals to bypass SMS firewalls commonly used to block phishing attempts.
Why iMessage and RCS?
iMessage and RCS offer features like file transfers and enhanced media support, making them appear more legitimate than traditional SMS messages. Additionally, these messaging services are often used for personal communication, potentially lowering a user’s guard against potential phishing attempts.
The Smishing Tactic
The Darcula platform facilitates smishing attacks, a form of phishing that uses text messages to trick victims. These messages often impersonate legitimate organizations, such as postal services, and typically lure users into clicking malicious links or providing sensitive information.
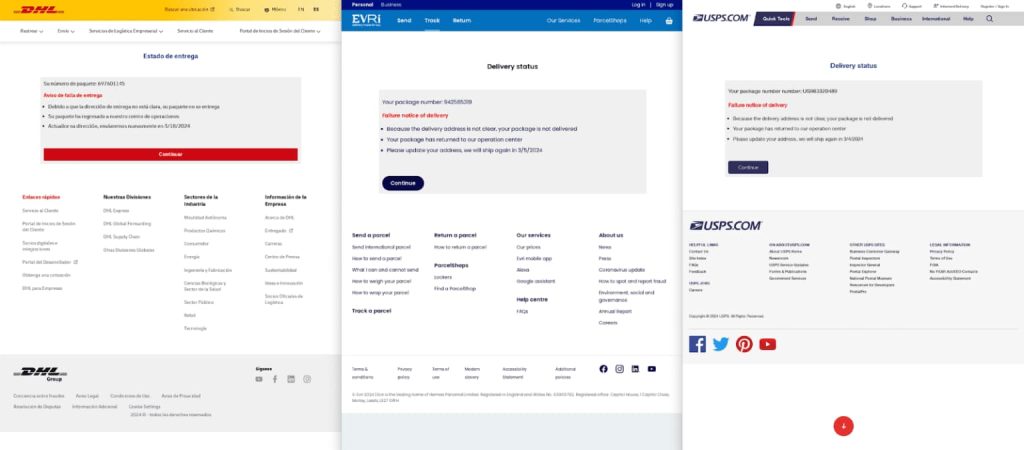
In the case of attacks targeting postal services, the messages might impersonate the USPS or a similar national postal service, informing recipients of missed deliveries or requesting additional information for package clearance. Clicking the malicious link could lead to a fake website designed to steal the user’s login credentials, credit card information, or other sensitive data.
Global Reach and Long History
The Netcraft report reveals that Darcula has been operational for at least a year and has been used in attacks on users in the UK and the United States. The platform’s capacity to target postal services in over 100 countries highlights its global reach and the potential impact of these phishing campaigns.
Importance of Cybersecurity Training
While the use of iMessage and RCS introduces a new element to smishing attacks, basic security principles and training remain crucial in protecting oneself. Users should be wary of unsolicited messages, even those coming from seemingly familiar sources.
Phishing attempts often create a sense of urgency, urging users to click links or respond immediately. Taking a moment to verify the legitimacy of a message by contacting the sender directly through a verified phone number or website can help avoid falling victim to these scams.
According to Max Gannon, Cyber Intelligence Analysis Manager at Cofense, “Darcula, a very advanced phishing kit, paints a dire picture of phone-based phishing that individuals are not trained to avoid. This kit uses new techniques carefully designed to avoid security controls.“
“While this advanced phishing kit is problematic and avoids common security controls, a user trained properly to detect phishing emails should be just as likely to detect phishing messages on other platforms,“ Max emphasised.
“The existence of this kit emphasizes the importance of training individuals to be more vigilant across platforms. Even if a trained individual were to fall for the phishing attempt and click the link, the request for sensitive information like credit card details or SSNs should raise immediate concerns,“ he added.
RELATED TOPICS
[ad_2]
Source link