
Image credit — Google
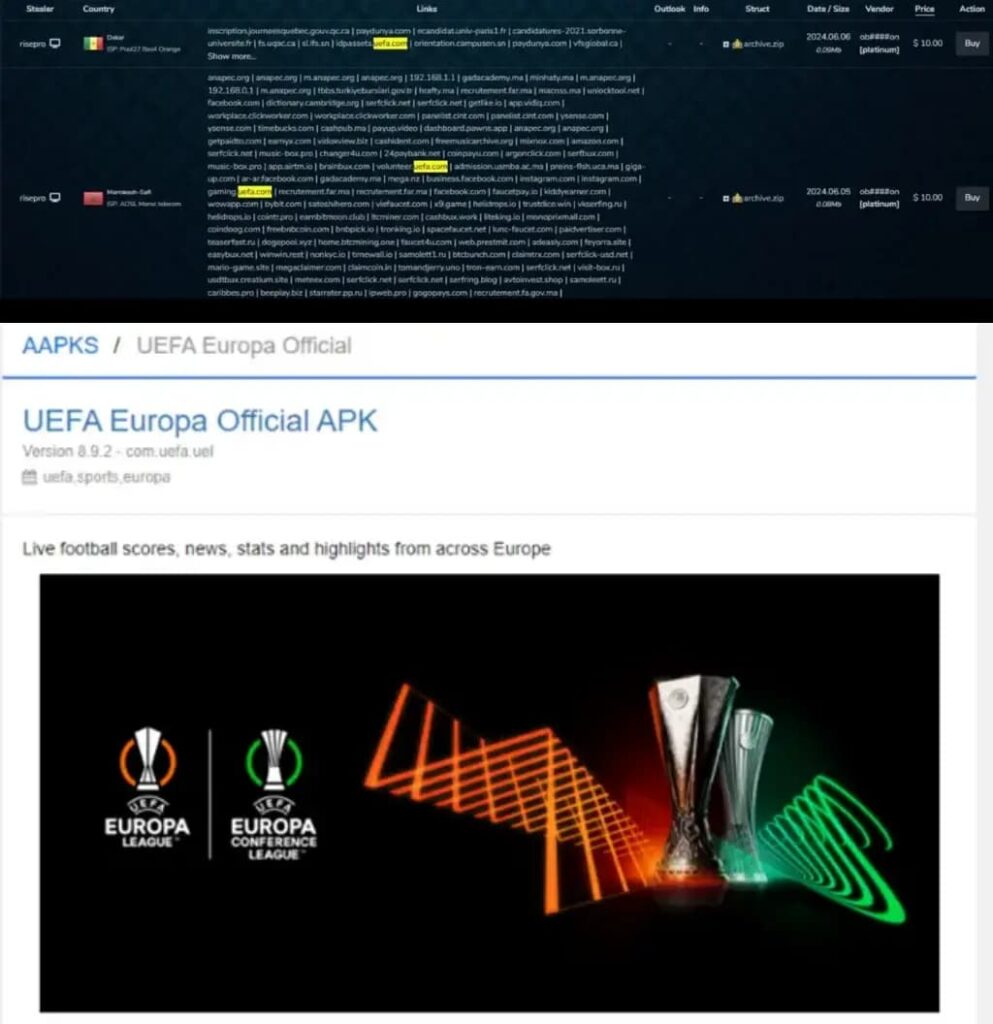
Google appears to be expanding access to its most advanced text-to-image AI model, Imagen 3. Originally announced last month with limited access, Google is believed to be planning early access to it for Gemini Advanced subscribers through a popup within the beta version of the Google app for Android.Spotted through an APK teardown, the app’s code reveals that Imagen 3 could become more widely available after its initial limited release. While there’s no definitive way to confirm if the updated model uses Imagen 3, it’s highly likely based on the app’s popup message.The popup header announces the “First look: Imagen 3” and invites Gemini Advanced subscribers to experience early access to the latest version of the AI tool. Additionally, a drop-down list outlines the updated features of this advanced AI model.
Imagen 3 as spotted in the latest beta of the Google app for Android and unofficially activated via code flags
| Images credit — AssembleDebug and Android Authority
The popup also provides information about the new and enhanced features available in the latest version of the AI tool, although the specifics of those features remain undisclosed. Initially, only select creators were granted access to Imagen 3 through a private preview, with others able to join a waitlist. Now, with this expanded access, Gemini Advanced subscribers will be given the opportunity to explore and test the capabilities of Imagen 3.The expanded access suggests that Google is progressively rolling out the model to a wider user base, starting with its Gemini Advanced subscribers. While the company hasn’t made an official announcement about this wider access, the discovery within the Google app for Android strongly indicates a broader release.
Although there’s no confirmation yet that the model is using Imagen 3, it seems highly probable given the available information. With this expanded access, users will be able to explore the latest advancements in AI-generated images and contribute to refining the model’s capabilities through their feedback and experiences.
[ad_2]
Source link






.webp)


