Who doesn’t like free trials? Prices are going up across just about all subscription services, so it’s great to be able to sample services to see if they’re fit for you. Amazon Prime Day is fast approaching, and the company has a honey of a deal for people looking to sample Amazon Music. For a limited time, users can get up to five free months of Amazon Music Unlimited.
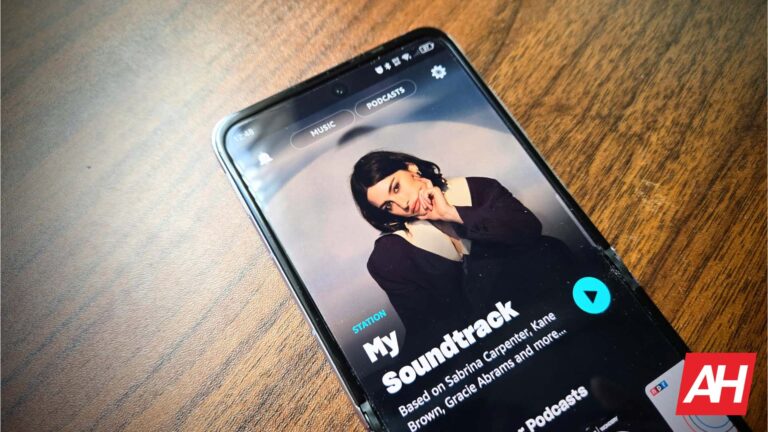
What’s Amazon Music Unlimited? This is the service that grants you access to similar features as Spotify, YouTube Music, Tidal, etc. You have access to the full catalog of Music provided through Amazon. You’ll be able to hear all of the latest music from today’s top artists. Also, if you’re in the mode for some classics, there’s a huge catalog of music from the olden days. Anything from the late 20th century to the late 17th century.
Along with that, you’ll be able to download tracks for offline listening. If you don’t like ads, well you’ll have ad-free listening. Topping off the list of features, you’ll gain access to HD music and spatial audio. This is one of the best services to get if you’re tightly wrapped in the Amazon ecosystem of products.
Get up to five free months of Amazon Music Unlimited
So, what does Amazon Music Unlimited have that other services don’t have? Well, you’ll have almost half a year to find out! The company has a deal that will give you a five-month free trial, but there’s a bit of a catch. Follow the link to be taken to the Amazon Music Store.
Get your Amazon Music Unlimited free trial!
You’ll get a five-month free trial if you’re an Amazon Prime subscriber. The service is usually $4.99/month for Prime subscribers. However, if you’re not a Prime subscriber, you’re still not left out in the rain. Non-Prime members will get three months of free Amazon Music Unlimited. They’ll still gain access to all of the features.
So, you won’t be able to use it for quite as long, but three months is still a pretty sweet deal. A regular Amazon Music subscription normally costs $10.99/month for non-Prime users.
[ad_2]
Source link