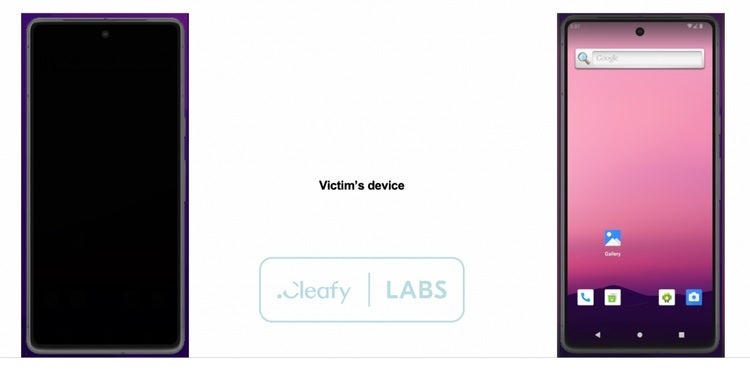
After nearly a year of lying low, the Medusa banking trojan for Android has resurfaced on security researchers’ radar. Cybersecurity firm Cleafy Threat Intelligence recently detected fresh campaigns targeting users in Europe and North America, including the US. The attackers have deployed more compact variants of the malware, allowing them to operate more stealthily.
New Medusa banking trojan campaigns pose grave threats to Android users
Medusa, aka TangleBot, is an Android banking trojan operating as a malware-as-a-service (MaaS). Discovered in 2020, the malware provides attackers with powerful tools to remotely initiate unauthorized financial transactions from infected phones. It boasts features such as keylogging—it can track key presses when you type, allowing threat actors to steal logging credentials. The malware can also control the screen and manipulate text messages.
The latest Medusa Android banking trojan campaigns began in May 2024, or at least that is when Cleafy researchers started tracking the new activities. This is the first activity of the trojan since July 2023, the cybersecurity firm reports. As pointed out by Bleeping Computer, the banking trojan is different from “the ransomware gang and the Mirai-based botnet for distributed denial-of-service (DDoS) attacks” of the same name (Medusa).
According to Cleafy, the new campaigns deploy upgraded variants of the banking trojan. These variants are more compact and require fewer permissions to perform the same malicious activities on an infected Android phone. They also boast new features such as full-screen overlaying and screenshot capturing, which make the trojan more powerful than ever. It can initiate fraudulent transactions directly from the device without the user’s knowledge.
Clefy discovered the activities of the Medusa banking trojan in Canada, France, Italy, Spain, Turkey, the UK, and the US. The criminal minds behind the campaigns rely on smishing (SMS phishing) to trick Android users into side-loading the malware. They distributed the malware through dropper apps, with the security firm identifying 24 campaigns delivering malicious apps via five separate botnets (UNKN, AFETZEDE, ANAKONDA, PEMBE, and TONY).
Dropper apps include a fake Chrome browser
Among the dropper apps used in these Medusa banking trojan campaigns are a fake Chrome browser and a fake streaming app called 4K Sports. The latter appears to be a well-planned bait as the UEFA EURO 2024 football/soccer championship is currently underway in Europe. Unsuspecting users would install it hoping to watch the championship live on their phone, only to potentially fall prey to devastating malware attacks that could wipe out their bank accounts.

Despite a reduced footprint—the malware authors removed 17 commands and several permission requests from the previous version—Medusa banking trojan still requires access to Android’s Accessibility Services and retains its capability to send text messages and access the contact list. Overall, it has become more powerful and more difficult to detect. The malware’s target scope has gotten bigger, potentially opening it up to wider deployment.
As of this writing, Cleafy Threat Intelligence hasn’t discovered any dropper app for the Medusa banking trojan on the Google Play Store. Google’s security measures seem to be doing their work effectively. This means you are safe as long as you don’t download and install dubious apps from the web, particularly from links received in messages from unknown numbers. You should download apps only from official app stores and official company websites.

[ad_2]
Source link