Image credit — Google
Google’s Pixel Recorder app, known for its transcription capabilities, has received a significant boost in functionality with the June Feature Drop. Alongside enhancements to the Summarize feature, a new app shortcut has been added for even quicker access.As spotted by 9to5Google, Pixel users can now create a shortcut on their home screens to instantly start a new recording. The shortcut appears as a red circle on a white background, similar to the floating action button (FAB) within the app. This update not only offers a more convenient way to start recordings but also brings it on par with the Quick Settings Tile functionality.
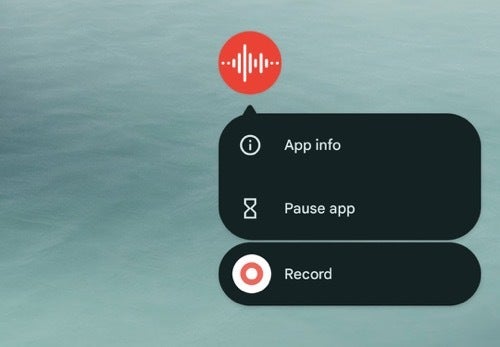
Image credit — 9to5Google
This June update isn’t just about convenience, though, as it also extends the Summarize feature to the Pixel 8 and Pixel 8a, which was previously exclusive to the Pixel 8 Pro. By enabling the Gemini Nano model in Developer options, users of these devices can now benefit from automatically generated summaries of their recordings. What’s more, these summaries are now capable of identifying and labeling speakers within the conversation, enhancing their accuracy and usefulness.The Summarize feature’s speaker identification works in conjunction with the manual Speaker Labels that users can set. This means you can either let the app automatically detect and label speakers, or take control and assign labels yourself for greater precision.The updated Pixel Recorder app, version 4.2.20240502.639621645, is currently rolling out to Pixel users through the Play Store. This update is a noteworthy advancement as it comes ahead of Apple’s introduction of live audio transcription in Notes and Voice Memos with iOS 18.
In terms of features, the June Feature Drop for Pixel Recorder brings a host of improvements. Whether it’s the added convenience of a home screen shortcut, the expanded availability of the Summarize feature, or the enhanced speaker identification within summaries, Pixel users now have an even more powerful tool for recording and transcribing their conversations.
[ad_2]
Source link


.webp)
.webp)
.webp)
.webp)


.webp)
.webp)