Not all system updates mean well, and some will even trick you into installing malware.
Malvertising seems to be enjoying a renaissance as of late, whether it is from ads on search engine results pages or via popular websites. Because browsers are more secure today than they were 5 or 10 years ago, the attacks that we are seeing all involve some form of social engineering.
A threat actor is using malicious ads to redirect users to what looks like a Windows security update. The scheme is very well designed as it relies on the web browser to display a full screen animation that very much resembles what you’d expect from Microsoft.
The fake security update is using a newly identified loader that at the time of the campaign was oblivious to malware sandboxes and bypassed practically all antivirus engines. We wrote a tool to ‘patch’ this loader and identified its actual payload as Aurora stealer. In this blog post, we detail our findings and how this campaign is connected to other attacks.
A convincing “system update”
Windows users are quite familiar with system updates, often interrupting hours of work or popping up in the middle of an intense game. When that happens, they just want to install whatever needs to be installed and get on with their day.
A threat actor is buying popunder ads targeting adult traffic and tricking victims with what appears to a system security update.

Figure 1: A fake system update hijacks the screen
As convincing as it looks, what you see above is actually a browser window that is rendered in full screen. This becomes more obvious when downloading the update file named ChromeUpdate.exe.
 Figure 2: The ‘Chrome update’ downloaded from the web browser
Figure 2: The ‘Chrome update’ downloaded from the web browser
Fully Undetectable (FUD) malware
While the file name appears as ChromeUpdate.exe, it uses the Cyrillic alphabet such that certain characters look similar but are different on disk. Its hex representation is %D0%A1hr%D0%BEm%D0%B5U%D1%80d%D0%B0t%D0%B5.exe as can be seen in the image below:

Figure 3: Hex encoding and Cyrillic alphabet
When we first ran the sample into a sandbox, we could not see anything obvious or that it was even malicious. The file would simply run and exit quickly. Over a couple of weeks, we collected nine different samples that looked more or less the same.
We also noticed that the threat actor was uploading each of his new builds to VirusTotal, a service owned by Google, to check if they were being detected by antivirus engines. The first user to submit each new sample always uploaded them from Turkey (country code TR) and in many instances the file name looked like it had come fresh from the compiler (i.e. build1_enc_s.exe).

Figure 4: User submissions to VirusTotal
While VirusTotal is no replacement for a full endpoint security product, with its 70 AV engines it is usually a good indicator to quickly check if a file is malicious or not. For more than 2 weeks, the samples had 0 detection on VT and it wasn’t until a blog post by Morphisec that detections started to appear. This new loader is called Invalid Printer and so far appears to have been used exclusively by this threat actor to bypass security products.

Figure 5: VirusTotal detections coincide with blog release
We actually stumbled upon Morphisec’s blog thanks to Threatray which identified similarities with a file we submitted to their sandbox. The service’s built-in OSINT identified similar samples and linked them with security articles.
 Figure 6: Threatray analysis page
Figure 6: Threatray analysis page
Patching the loader
Invalid Printer performs a check on the computer’s graphic card and specifically its vendor ID which it compares against known manufacturers such as AMD, NVidia. Virtual machines and sandboxes in general do not use real hardware and will fail to pass the check.
We were able to patch the samples we had collected and identify their payload. The patch consists of replacing the graphics card check with a random number and always returning true, therefore allowing the file to run in any sandbox.
 Figure 7: Python script to patch loader
Figure 7: Python script to patch loader
The automated malware unpacking service from OpenAnalysis UnpacMe now supports properly unpacking samples using the Invalid Printer loader. It allowed us to determine what malware family is being distributed as well as indicators of compromise. For example, one of our samples (31c425510fe7f353002b7eb9d101408dde0065b160b089095a2178d1904f3434) has the same command and control server (94.142.138[.]218) as one mentioned in Morphisec’s blog.
 Figure 8: UnpacMe results page
Figure 8: UnpacMe results page
In this specific malvertising campaign, the payload used was the Aurora Stealer, a popular piece of malware that is designed to harvest credentials from systems.
Campaign stats
The threat actor is using a panel to track high level stats about visitors to the fake system update web page. Based on the numbers from this panel, there were 27,146 potential unique victims and 585 of them downloaded the malware during the past 49 days.

Figure 9: Panel showing browser visits and downloads

Figure 10: Browser user-agents, IP addresses and geolocation
War and Russia references
We believe there is a single threat actor behind this malvertising campaign and others such as the one Morphisec uncovered. The malware author seems to take a very high interest in creating FUD malware and constantly uploads it to VirusTotal to verify, always using the same submitter profile.
We couldn’t help but notice a possible reference to the war in Ukraine left within the fake Chrome Update page and commented out:
 Figure 11: Commented HTML code
Figure 11: Commented HTML code
Some of the websites belonging to this threat actor were not loading malware but instead had a single YouTube video promoting the cities and landscapes of Russia:
 Figure 12: YouTube video about Russia in 12K HDR
Figure 12: YouTube video about Russia in 12K HDR
Additionally, we found some connections with tech support scams and even an Amadey panel that also appears to belong to the threat actor.
Protection
Malwarebytes already protected users from this malvertising campaign by blocking the malicious ads involved. We detect the payloads as Spyware.Aurora.


Special thanks to Roberto Santos for help with the sample and binary patching.
Indicators of Compromise
Malvertising gate
qqtube[.]ru
194.58.112[.]173
Fake system update page
activessd[.]ru
chistauyavoda[.]ru
xxxxxxxxxxxxxxx[.]ru
activehdd[.]ru
oled8kultra[.]ru
xhamster-18[.]ru
oled8kultra[.]site
activessd6[.]ru
activedebian[.]ru
shluhapizdec[.]ru
04042023[.]ru
clickaineasdfer[.]ru
moskovpizda[.]ru
pochelvpizdy[.]ru
evatds[.]ru
click7adilla[.]ru
grhfgetraeg6yrt[.]site
92.53.96[.]119
Invalid Printer samples
d29f4ffcc9e2164800dcf5605668bdd4298bcd6e75b58bed9c42196b4225d590
5a07e02aec263f0c3e3a958f2b3c3d65a55240e5da30bbe77c60dba49d953b2c
193cec31ea298103fe55164ff6270a2adf70248b3a4d05127414d6981f72cef4
dac1bd40799564288bf55874543196c4ef6265d89e3228864be4d475258b9062
40b8acc3560ac0e1825755b3b05ef01c46bdbd184f35a15d0dc84ab44fa99061
31c425510fe7f353002b7eb9d101408dde0065b160b089095a2178d1904f3434
398faa3aab8cce7a12e3e3f698bc29514c5b10a4369cc386421913e31f95cfdc
93b9199ca9e1ee0afbe7cf6acccedd39f37f2dd603a3b1ea05084ab29ff79df7
4c80bd604ae430864c507d723c6a8c66f4f5e9ba246983c833870d05219bd3e5
Aurora Stealer C2
103.195.103[.]54:443
94.142.138[.]218:4561
Amadey Stealer panel
193.233.20[.]29/games/category/Login.php
Malwarebytes removes all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.
TRY NOW


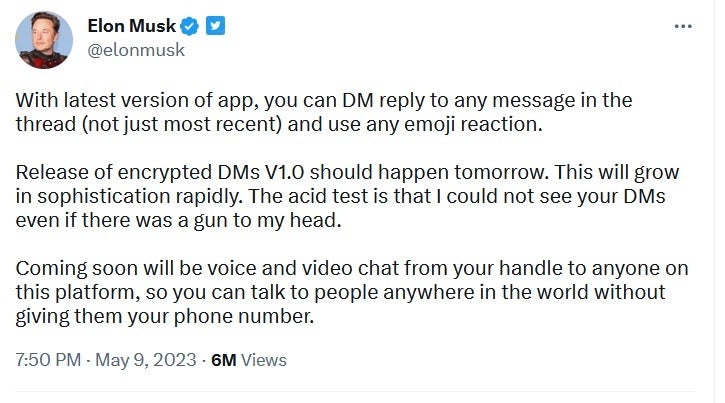



















 Figure 2: The ‘Chrome update’ downloaded from the web browser
Figure 2: The ‘Chrome update’ downloaded from the web browser


 Figure 6: Threatray analysis page
Figure 6: Threatray analysis page Figure 7: Python script to patch loader
Figure 7: Python script to patch loader Figure 8: UnpacMe results page
Figure 8: UnpacMe results page

 Figure 11: Commented HTML code
Figure 11: Commented HTML code Figure 12: YouTube video about Russia in 12K HDR
Figure 12: YouTube video about Russia in 12K HDR 
