Having this option should help put some order into the chaos that is the Google Photos library, but won’t completely disappear distracting items like screenshots or memes. What it does, is that it tucks them away in their designated albums where you can find them if needed. The primary difference is that they won’t invade your main photo grid while you’re trying to reminisce. These changes were found hidden in Google Photos version 6.79.0.624777117 with the below strings:
<string name=”photos_allphotos_gridcontrols_hide_clutter_base_filter_setting_title”>Hide clutter</string>
<string name=”photos_allphotos_gridcontrols_hide_clutter_base_filter_setting_subtitle”>Backed-up photos like screenshots, GIFs, and memes are hidden</string>
Memories are getting a makeover too
The Google Photos’ Memories tab is also getting a fresh coat of paint. The current collage-like presentation will make way for a more streamlined interface. Individual memories will now be shown as rounded rectangles, each with a single representative photo. Whether you love or hate the change, it’s definitely a shift in Google’s approach to presenting those nostalgic moments.
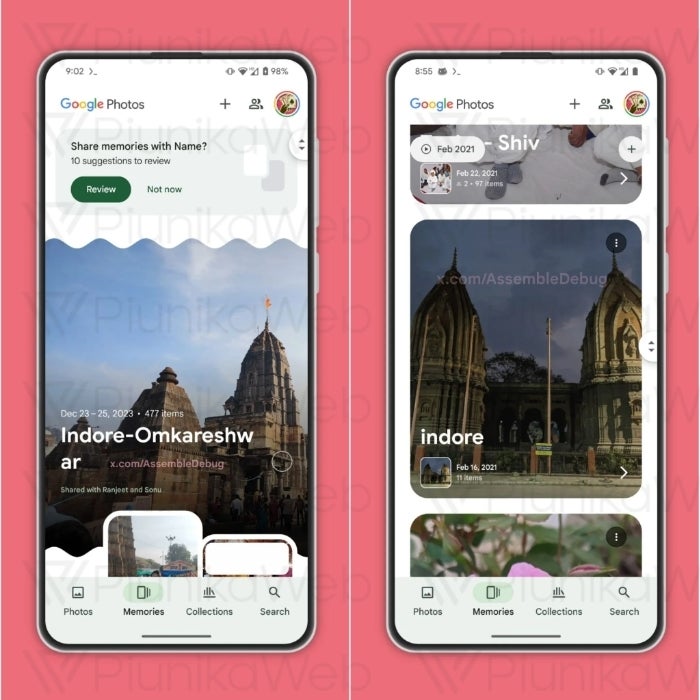
Google Photos’ Memories before and after | Source: PiunikaWeb
A bit more personalization
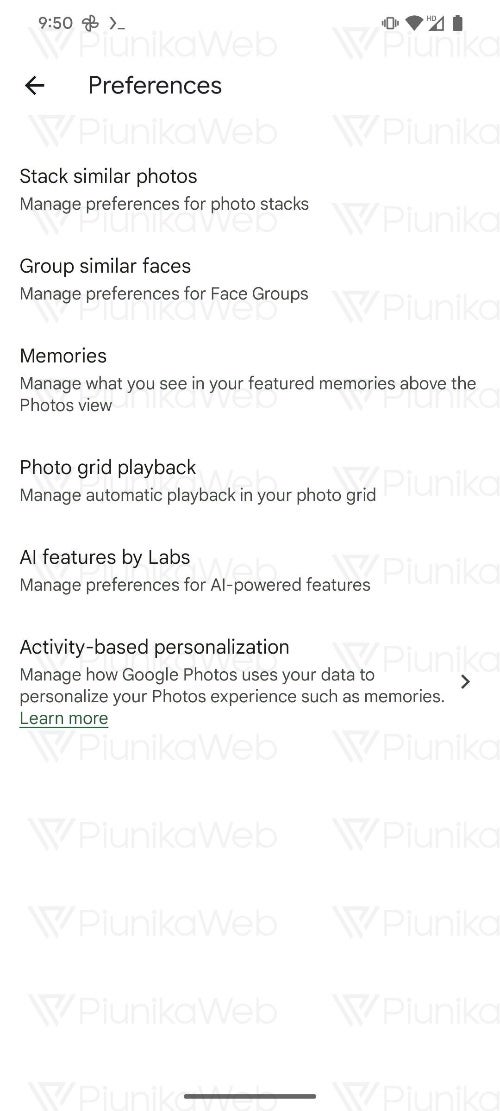
Google is also sneaking in a small but welcome tweak to its AI feature suggestions. Sometimes, the AI-generated Memory titles offered by Google Photos can be less than ideal. A new toggle in the app settings will let users disable these suggestions if they wish, allowing for more control over how their memories are labeled.Source: PiunikaWeb
It’s important to remember that these features are still under development, so they may change at any time or may not even roll out at all. Still, it’s encouraging to see Google Photos continuing to evolve and offer users more control over their digital photo libraries.
[ad_2]
Source link