The advent of blockchain technology and smart contracts has opened new avenues for handling transactions across various industries. In the realm of personal injury law, these innovations are starting to significantly alter how settlements are managed. Blockchain’s inherent characteristics of transparency, security, and immutability, coupled with smart contracts’ ability to execute agreements automatically, pave the way for a more streamlined and efficient settlement process. The potential for reducing the time and resources currently required for dispute resolution and payment distribution is considerable.
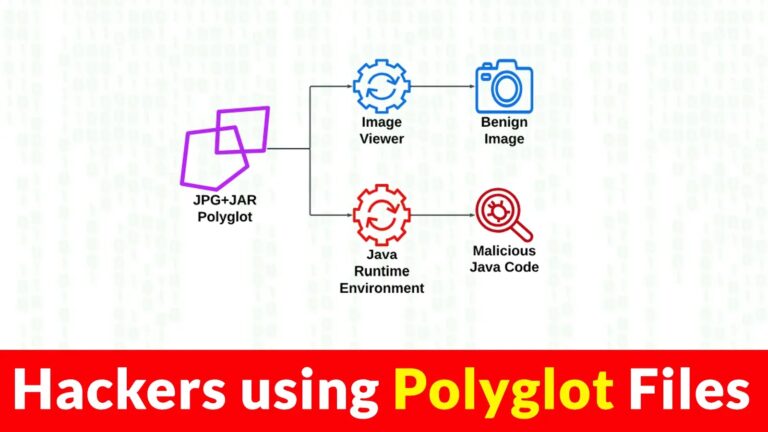
Smart contracts, self-executing contracts with the terms directly written into code, offer a transformative approach to managing and enforcing settlements. They work by automating the release of funds when certain predefined conditions are met, minimizing the need for intermediaries typically involved in the settlement process. This automation can greatly reduce administrative overhead and the risk of human error, leading to faster and more reliable resolution of claims for all parties involved.
Blockchain Technology in Personal Injury Settlements
Blockchain technology introduces a transformative approach to handling settlements in personal injury cases, particularly within the scopes of medical malpractice and products liability. It offers a secure, transparent, and efficient method of managing transactions and contractual obligations.
Understanding Blockchain Basics
Blockchain is a digitally distributed ledger that records transactions across many computers. Its primary features include immutability and decentralization, which assure that once information is recorded, it cannot be altered retroactively. This is particularly relevant for an Aurora personal injury lawyer, who can ensure the integrity of evidence and transaction records in personal injury cases.
The Role of Smart Contracts
Smart contracts are self-executing contracts with the terms of the agreement between buyer and seller directly written into lines of code. They run on blockchain, and their execution is automatic when certain conditions are met. This means, for personal injury claims in Aurora, settlements can be dispensed swiftly and without bias upon meeting predefined criteria, reducing the time and complications often associated with such legal proceedings.
Advantages for Legal Practitioners:
– Automatic enforcement of contract terms
– Reduction in the likelihood of disputes
– Streamlining of case management processes
Implications for Medical Malpractice and Products Liability Cases
In the context of medical malpractice, blockchain can seamlessly integrate with electronic health records to securely and permanently document patient care transactions, ensuring that all information pertaining to a case is unalterable and transparent. For products liability cases, blockchain can track a product’s lifecycle from production to sale, which aids in pinpointing responsibility in the event of a claim.
Benefits for Stakeholders:
– Clients: Empowers them with definitive evidence in cases.
– Lawyers: Facilitates a higher trust level in the case’s documentation.
– Healthcare Providers and Manufacturers: Encourages accountability and improvements in patient care and product quality.
Blockchain technology stands to make substantial improvements over traditional methods of managing personal injury cases, lending assuredness and precision to the intricate legal processes.
Enhancing Legal Practice with Smart Contracts
Smart contracts are transforming the traditional legal practice by automating and enforcing the settlement process in litigation, particularly in personal injury cases. This technology offers a distinct advantage for an injury attorney and their firms, streamlining operations and ensuring transparency.
Smart Contracts in Litigation Processes
Smart contracts can significantly reduce the time and resources required during litigation by automating the settlement agreement terms. They function as self-executing contracts with the terms of the agreement written into code and existing on a blockchain. This means that once the prescribed conditions are met, the smart contract executes the relevant actions automatically.
Injury attorneys can leverage smart contracts to handle escrow arrangements, where settlement amounts are released only after specified conditions are met. For example, payments can be contingent upon the client’s receipt of medical treatment or submission of necessary documentation, with each step verifiably recorded on the blockchain.
Benefits for Injury Attorneys and Law Firms
Law firms that adopt smart contracts in their legal processes can benefit in several ways:
– Automation: Reducing the need for manual oversight in the execution of agreements.
– Efficiency: Streamlining the settlement process can lead to faster resolutions.
– Transparency: Immutable record-keeping on a blockchain provides clear evidence of executed terms.
Injury attorneys, in particular, will find that the technology enables them to focus more on case strategies and client interaction, rather than administrative tasks.
Case Study: Agruss Law Firm’s Innovative Approach
Agruss Law Firm, known for its personal injury advocacy, has implemented smart contracts to better serve its clients. The firm has developed a system where settlements are handled through smart contracts, allowing for prompt and undisputed distribution of funds.
The firm’s use of smart contracts presents:
– Client Satisfaction: Clients enjoy the speedy receipt of funds without the usual bureaucratic delays.
– Operational Efficiency: The firm saves on administrative costs, passing savings to clients and investing more in case preparation.
By adopting smart contracts, Agruss Law Firm has set a precedent for how personal injury settlements can be managed effectively in the digital age.
Featured image source


.webp)
.webp)
.webp)

.webp)
.webp)
.webp)
.webp)
