An Indian student used ChatGPT, a fake website, a phony teacher email address, and forged documents to scam a US scholarship! His bragging on Reddit led to his downfall. How did a moderator expose the elaborate scheme?
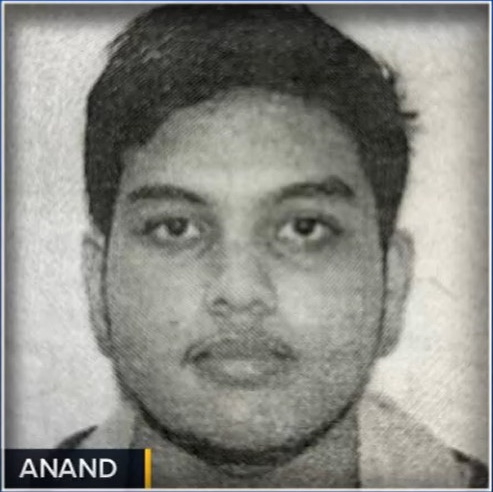
Aryan Anand, a 19-year-old Indian student has been expelled from Lehigh University and is set to be deported after his highly sophisticated fraud was uncovered through a Reddit post, thanks to a moderator.
Anand, who managed to secure a full scholarship to the university, ranked #47 in National Universities in the US, fabricated documents, including a fake death certificate for his father, to facilitate his admission and financial aid.
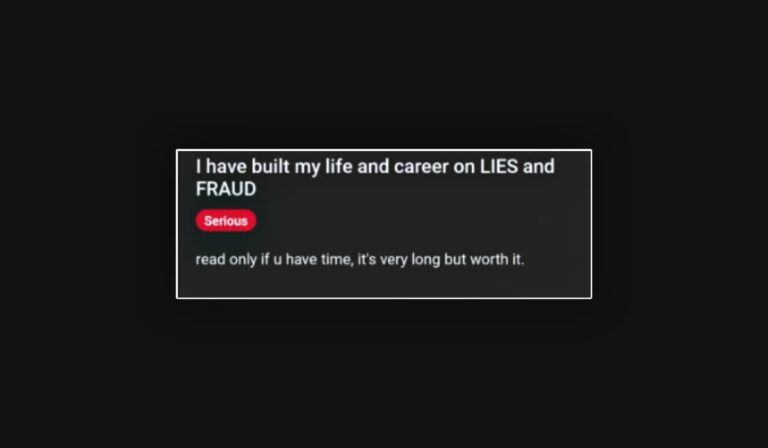
Aryan Anand’s fraudulent activities came to light when he anonymously posted on Reddit under u/TransportationOk4728, boasting about his achievements in a thread titled “I have built my life and career on lies and fraud.”
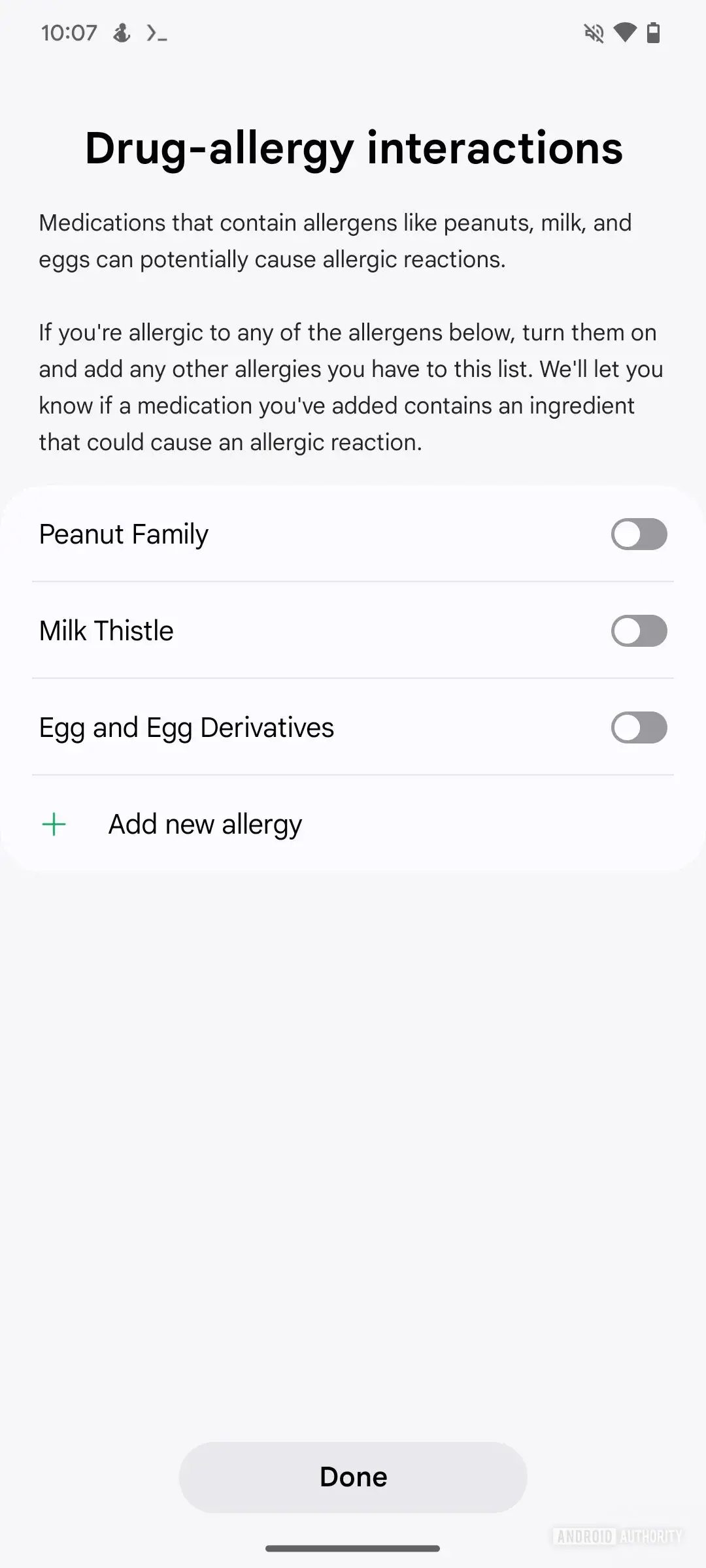
The now-deleted post detailed how Anand forged his Class 12 transcripts, created a fake school domain and email addresses mimicking his school principal, and used AI tools like ChatGPT to craft his admission essays and pass exams.
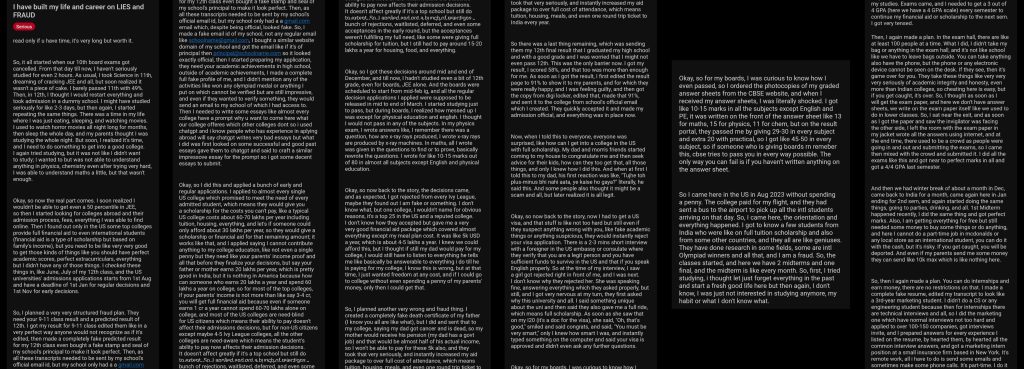
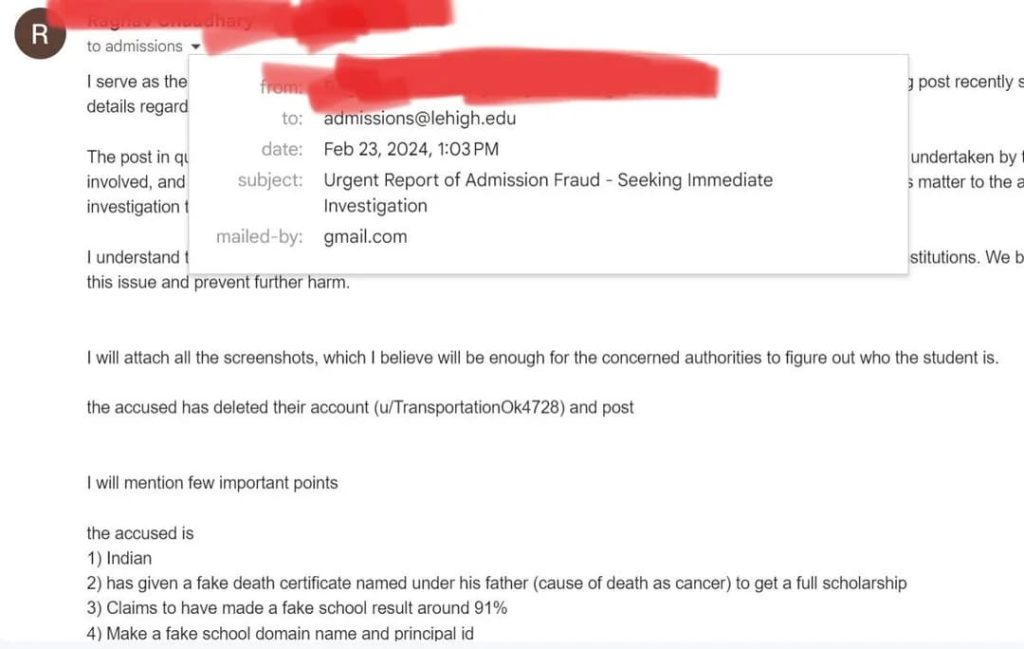
The confession caught the attention of a vigilant Reddit moderator, who delved deeper into Anand’s claims. The moderator’s investigation revealed that Anand was a student at Lehigh University, prompting them to alert the university authorities. This led to an internal probe by Lehigh University, resulting in Anand’s arrest on April 30, 2024, and his subsequent expulsion and deportation.
Anand’s Reddit post, where he blatantly detailed his methods and boasted about his success, became his undoing. Users expressed mixed reactions, with some condemning his actions and others expressing disbelief at the extent of his deception.
“My man was an absolute genius, a dumbass, a foreshadower all at the same time. Dude, it just felt like I read a movie script of something,” one user commented, illustrating that the Reddit community took this incident not just as news but as a compelling plot line for a movie.
Another user expressed the reality of the situation, speculating the implications this incident is likely to have on the US college admissions process:
“F*** this guy, took advantage of kind-hearted people and his actions will now most likely make the admission process much more difficult for everyone else. There is no smartness in faking your father’s death, just malice and greed. Just a risky spoiled brat who got lucky in his actions.”
The moderator who discovered Anand’s identity provided crucial evidence to Lehigh University, leading to a comprehensive investigation by the Lehigh University Police Department. Anand was charged with multiple felonies, including forgery, tampering with records, and theft by deception.
On June 12, 2024, he pleaded guilty to forgery and was sentenced to one to three months in Northampton County Prison, equivalent to time served. As part of a plea deal, he agreed to return to India, and the university decided not to pursue restitution of the $85,000 (approximately ₹70 lakh) scholarship funds.
As Anand prepares to return to India, his story serves as a cautionary tale about the perils of academic dishonesty and the power of digital communities to uncover the truth.
RELATED TOPICS
- 2 students arrested for disrupting school WiFi to skip exam
- 13-year-old student arrested for hacking school computers
- Indian call center seized over Amazon hacking of US citizens
- Student hacks school’s computer system to alter grades, GPA
- Indian Ex-Employee Jailed for Wiping Virtual Servers in Singapore
[ad_2]
Source link




.webp)
.webp)
.webp)
.webp)